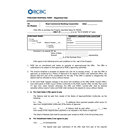
| 541 |
2024-08-28 12:28
|
wecreatebuttermilkchocolateicr... 61b061a48eb132e15884e4b53cf0401f
MS_RTF_Obfuscation_Objects RTF File doc VirusTotal Malware Malicious Traffic exploit crash unpack itself Tofsee Exploit DNS crashed |
1
http://107.172.31.21/xampp/kkb/verynicebuttermilkchocolateicce.tIF
|
3
ia803104.us.archive.org(207.241.232.154) - malware
107.172.31.21 - mailcious
207.241.232.154 - malware
|
1
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
|
|
4.6 |
M |
33 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 542 |
2024-08-28 12:28
|
 MsMpEng.exe MsMpEng.exe bd36e9fc7144e50088bdcb08f842d4ae
Suspicious_Script_Bin Malicious Library UPX PE File PE32 DLL VirusTotal Malware Check memory Creates executable files unpack itself AppData folder |
|
|
|
|
2.8 |
M |
40 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 543 |
2024-08-28 12:26
|
 nnn.exe nnn.exe 0034cc280cf75d46ec0d9a7911228109
Antivirus UPX PE File .NET EXE PE32 OS Processor Check Lnk Format GIF Format VirusTotal Malware Telegram AutoRuns suspicious privilege MachineGuid Check memory Checks debugger Creates shortcut Creates executable files unpack itself Check virtual network interfaces AppData folder AntiVM_Disk VM Disk Size Check Tofsee Windows ComputerName DNS keylogger |
|
2
api.telegram.org(149.154.167.220) - mailcious
149.154.167.220 - mailcious
|
4
ET INFO TLS Handshake Failure
ET HUNTING Telegram API Domain in DNS Lookup
ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
|
|
6.6 |
|
59 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 544 |
2024-08-28 12:25
|
seethedifferentofcupcakewhichm... 603f3fc7d36b263a35aebc03ca35ee34
MS_RTF_Obfuscation_Objects RTF File doc VirusTotal Malware Malicious Traffic buffers extracted RWX flags setting exploit crash Tofsee Exploit DNS crashed |
1
http://198.46.178.137/890/wecancreatebuttersmooththingstobe.tIF
|
3
ia803104.us.archive.org(207.241.232.154) - malware
207.241.232.154 - malware
198.46.178.137 - malware
|
1
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
|
|
5.0 |
M |
35 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 545 |
2024-08-28 10:27
|
 66ce056ac07c2_crypted.exe#1 66ce056ac07c2_crypted.exe#1 b79ed7b267159f2b1497de63786e6f6d
RedLine stealer Antivirus ScreenShot PWS AntiDebug AntiVM PE File .NET EXE PE32 VirusTotal Malware PDB Code Injection Check memory Checks debugger buffers extracted unpack itself Windows DNS Cryptographic key |
|
1
|
|
|
10.0 |
M |
37 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 546 |
2024-08-28 10:24
|
 66ce111830a90_vrn12.exe#d12 66ce111830a90_vrn12.exe#d12 25629d287f7defb4e86755910b5926bf
Stealc Client SW User Data Stealer LokiBot ftp Client info stealer Antivirus Malicious Library Http API PWS HTTP Code injection Internet API AntiDebug AntiVM PE File .NET EXE PE32 FTP Client Info Stealer VirusTotal Malware Telegram PDB MachineGuid Code Injection Malicious Traffic Check memory Checks debugger buffers extracted WMI unpack itself Windows utilities Collect installed applications suspicious process malicious URLs sandbox evasion WriteConsoleW anti-virtualization installed browsers check Tofsee Windows Browser ComputerName DNS Software |
1
https://steamcommunity.com/profiles/76561199761128941 - rule_id: 42293
|
5
t.me(149.154.167.99) - mailcious
steamcommunity.com(23.222.161.105) - mailcious
149.154.167.99 - mailcious
94.130.188.148 - mailcious
184.87.103.42 - mailcious
|
3
ET INFO TLS Handshake Failure
ET INFO Observed Telegram Domain (t .me in TLS SNI)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
|
1
https://steamcommunity.com/profiles/76561199761128941
|
16.0 |
M |
38 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 547 |
2024-08-28 10:22
|
 saofewk.exe saofewk.exe a0a71a13e2ea5c606f46ced827fdc156
Stealc Client SW User Data Stealer LokiBot Gen1 ftp Client info stealer Generic Malware Downloader Antivirus Malicious Library UPX Malicious Packer ScreenShot Http API PWS Create Service Socket DGA Escalate priviledges Steal credential Sniff Browser Info Stealer Malware download FTP Client Info Stealer Vidar VirusTotal Email Client Info Stealer Malware c&c Telegram PDB MachineGuid Code Injection Malicious Traffic Check memory Checks debugger buffers extracted WMI Creates executable files unpack itself Windows utilities Collect installed applications suspicious process malicious URLs sandbox evasion WriteConsoleW anti-virtualization installed browsers check Tofsee Stealc Stealer Windows Browser Email ComputerName DNS Software plugin |
12
http://46.8.231.109/1309cdeb8f4c8736/nss3.dll
http://46.8.231.109/1309cdeb8f4c8736/msvcp140.dll
http://147.45.44.104/prog/66ce111e6839c_vsfdki.exe
http://46.8.231.109/1309cdeb8f4c8736/sqlite3.dll
http://46.8.231.109/c4754d4f680ead72.php - rule_id: 42211
http://46.8.231.109/1309cdeb8f4c8736/vcruntime140.dll
http://46.8.231.109/1309cdeb8f4c8736/softokn3.dll
http://46.8.231.109/1309cdeb8f4c8736/mozglue.dll
http://46.8.231.109/ - rule_id: 42142
http://147.45.44.104/prog/66ce11214efea_lfhnsda.exe
http://46.8.231.109/1309cdeb8f4c8736/freebl3.dll
https://steamcommunity.com/profiles/76561199761128941 - rule_id: 42293
|
7
t.me(149.154.167.99) - mailcious
steamcommunity.com(184.85.65.125) - mailcious
149.154.167.99 - mailcious
147.45.44.104 - malware
94.130.188.148 - mailcious
184.87.103.42 - mailcious
46.8.231.109 - mailcious
|
21
ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in
ET MALWARE Win32/Stealc Requesting browsers Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with browsers Config M1
ET MALWARE Win32/Stealc Requesting plugins Config from C2
ET MALWARE Win32/Stealc/Vidar Stealer Active C2 Responding with plugins Config M1
ET INFO Dotted Quad Host DLL Request
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET MALWARE Win32/Stealc Submitting System Information to C2
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET DROP Spamhaus DROP Listed Traffic Inbound group 23
ET INFO Executable Download from dotted-quad Host
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO TLS Handshake Failure
ET INFO Observed Telegram Domain (t .me in TLS SNI)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
|
3
http://46.8.231.109/c4754d4f680ead72.php
http://46.8.231.109/
https://steamcommunity.com/profiles/76561199761128941
|
18.0 |
M |
26 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 548 |
2024-08-28 10:21
|
 66cdfc485c6f9_instruction.exe#... 66cdfc485c6f9_instruction.exe#... 0a7f5d0b4dab9c77dc68db0ea99b0058
Emotet Malicious Library UPX PE File .NET EXE PE32 VirusTotal Malware PDB Check memory Checks debugger unpack itself ComputerName Remote Code Execution |
|
|
|
|
3.2 |
M |
25 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 549 |
2024-08-28 10:19
|
 Underldighedens.vbs Underldighedens.vbs 9f920797b154f49ea9e2bcaea7e8607f
Generic Malware Antivirus powershell suspicious privilege Check memory Checks debugger Creates shortcut unpack itself Windows utilities Check virtual network interfaces suspicious process WriteConsoleW Tofsee Windows ComputerName Cryptographic key |
|
2
softiq.ro(194.36.140.235) - mailcious
194.36.140.235 - mailcious
|
3
SURICATA TLS invalid record type
SURICATA TLS invalid record/traffic
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
|
|
7.0 |
|
|
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 550 |
2024-08-28 10:18
|
 66ce0aa740197_1112.exe 66ce0aa740197_1112.exe 861faba8e780fc1f323eb46f390fb6ca
Malicious Library UPX PE File PE32 OS Processor Check VirusTotal Malware unpack itself Remote Code Execution |
|
|
|
|
1.8 |
M |
29 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 551 |
2024-08-28 10:17
|
 66ce1679b8344_Main.exe 66ce1679b8344_Main.exe eb0830efaf21e7e426eb602118f70c62
Emotet Generic Malware Suspicious_Script_Bin Downloader Malicious Library UPX Malicious Packer Create Service Socket DGA Http API ScreenShot Escalate priviledges Steal credential PWS Hijack Network Sniff Audio HTTP DNS Code injection Internet API persiste VirusTotal Malware suspicious privilege Code Injection Check memory Checks debugger Creates executable files Windows utilities malicious URLs AntiVM_Disk WriteConsoleW VM Disk Size Check Windows |
|
|
|
|
5.2 |
M |
10 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 552 |
2024-08-28 10:15
|
 66ce237125ba7_vjrew2ge.exe#spa... 66ce237125ba7_vjrew2ge.exe#spa... 985591b59446fcf5dadd314fdbda90e4
Stealc Client SW User Data Stealer LokiBot ftp Client info stealer Antivirus Malicious Library Http API PWS HTTP Code injection Internet API AntiDebug AntiVM PE File .NET EXE PE32 FTP Client Info Stealer VirusTotal Malware Telegram PDB MachineGuid Code Injection Malicious Traffic Check memory Checks debugger buffers extracted WMI unpack itself Windows utilities Collect installed applications suspicious process malicious URLs sandbox evasion WriteConsoleW anti-virtualization installed browsers check Tofsee Windows Browser ComputerName DNS Software |
1
https://steamcommunity.com/profiles/76561199761128941 - rule_id: 42293
|
5
t.me(149.154.167.99) - mailcious
steamcommunity.com(184.85.65.125) - mailcious
149.154.167.99 - mailcious
94.130.188.148 - mailcious
184.87.103.42 - mailcious
|
3
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Observed Telegram Domain (t .me in TLS SNI)
ET INFO TLS Handshake Failure
|
1
https://steamcommunity.com/profiles/76561199761128941
|
15.8 |
M |
39 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 553 |
2024-08-28 10:15
|
 66ce1115726ee_vjweiq15.exe#d15 66ce1115726ee_vjweiq15.exe#d15 4aecaf0aad3b9c42ea948554a7cae1a7
Stealc Client SW User Data Stealer LokiBot ftp Client info stealer Antivirus Malicious Library Http API PWS HTTP Code injection Internet API AntiDebug AntiVM PE File .NET EXE PE32 FTP Client Info Stealer VirusTotal Malware Telegram PDB MachineGuid Code Injection Malicious Traffic Check memory Checks debugger buffers extracted WMI unpack itself Windows utilities Collect installed applications suspicious process malicious URLs WriteConsoleW anti-virtualization installed browsers check Tofsee Windows Browser ComputerName DNS Software |
1
https://steamcommunity.com/profiles/76561199761128941 - rule_id: 42293
|
5
t.me(149.154.167.99) - mailcious
steamcommunity.com(184.85.65.125) - mailcious
149.154.167.99 - mailcious
94.130.188.148 - mailcious
184.87.103.42 - mailcious
|
3
ET INFO TLS Handshake Failure
ET INFO Observed Telegram Domain (t .me in TLS SNI)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
|
1
https://steamcommunity.com/profiles/76561199761128941
|
15.4 |
M |
27 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 554 |
2024-08-28 10:14
|
 66ce162f61921_crypted.exe#1 66ce162f61921_crypted.exe#1 fc980ed1da175090e176c4c4b9b1fd01
Client SW User Data Stealer Gen1 ftp Client info stealer Generic Malware Antivirus Malicious Library UPX Malicious Packer Http API PWS AntiDebug AntiVM PE File .NET EXE PE32 DLL OS Processor Check Browser Info Stealer Malware download FTP Client Info Stealer Vidar VirusTotal Email Client Info Stealer Malware c&c PDB Code Injection Malicious Traffic Check memory Checks debugger buffers extracted Creates executable files unpack itself Collect installed applications sandbox evasion anti-virtualization installed browsers check Stealc Stealer Windows Browser Email ComputerName DNS Software plugin |
9
http://147.45.47.253/58b7620e0f34e81d/sqlite3.dll
http://147.45.47.253/58b7620e0f34e81d/vcruntime140.dll
http://147.45.47.253/58b7620e0f34e81d/softokn3.dll
http://147.45.47.253/58b7620e0f34e81d/msvcp140.dll
http://147.45.47.253/58b7620e0f34e81d/freebl3.dll
http://147.45.47.253/072aacac8f68fd5f.php
http://147.45.47.253/58b7620e0f34e81d/mozglue.dll
http://147.45.47.253/58b7620e0f34e81d/nss3.dll
http://147.45.47.253/
|
1
|
17
ET DROP Spamhaus DROP Listed Traffic Inbound group 23
ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in
ET INFO Dotted Quad Host DLL Request
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET MALWARE Win32/Stealc Requesting browsers Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with browsers Config M1
ET MALWARE Win32/Stealc Requesting plugins Config from C2
ET MALWARE Win32/Stealc/Vidar Stealer Active C2 Responding with plugins Config M1
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET MALWARE Win32/Stealc Submitting System Information to C2
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
ET MALWARE Win32/Stealc Submitting Screenshot to C2
|
|
14.2 |
|
27 |
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 555 |
2024-08-28 10:13
|
 vsfdki.exe vsfdki.exe 1004e31f8b0d72820d77e16371794c0e
Stealc Client SW User Data Stealer LokiBot ftp Client info stealer Antivirus Malicious Library Http API PWS HTTP Code injection Internet API AntiDebug AntiVM PE File .NET EXE PE32 FTP Client Info Stealer Malware Telegram PDB MachineGuid Code Injection Malicious Traffic Check memory Checks debugger buffers extracted WMI unpack itself Windows utilities Collect installed applications suspicious process malicious URLs WriteConsoleW anti-virtualization installed browsers check Tofsee Windows Browser ComputerName DNS Software |
1
https://steamcommunity.com/profiles/76561199761128941 - rule_id: 42293
|
5
t.me(149.154.167.99) - mailcious
steamcommunity.com(184.85.65.125) - mailcious
149.154.167.99 - mailcious
94.130.188.148 - mailcious
184.87.103.42 - mailcious
|
3
ET INFO Observed Telegram Domain (t .me in TLS SNI)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO TLS Handshake Failure
|
1
https://steamcommunity.com/profiles/76561199761128941
|
15.0 |
M |
|
ZeroCERT
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|