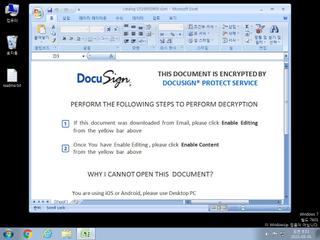
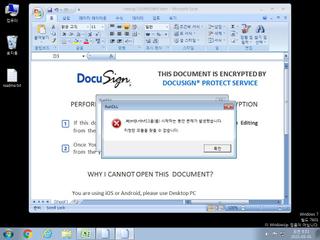
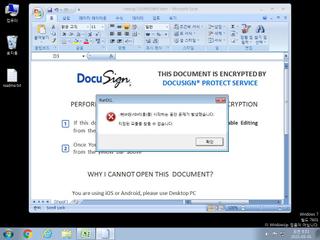
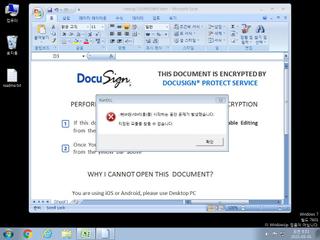
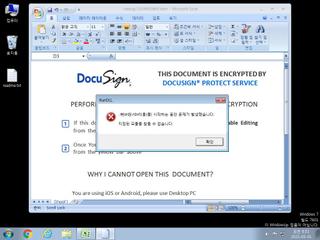
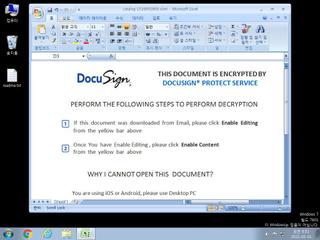
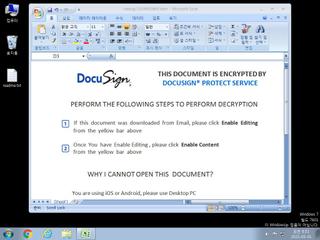
ScreenShot
| Created | 2021.05.01 08:53 | Machine | s1_win7_x6401 |
| Filename | catalog-1539950969.xlsm | ||
| Type | Microsoft Excel 2007+ | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 6 detected (XLSM, Sneaky, Camelot) | ||
| md5 | fbd50cca96787817cc8ec7c5895da104 | ||
| sha256 | 8a9caccaaa94d1f1d3cdc18ddc6e0289f68d42bf913ddaa8891a861bf12ca337 | ||
| ssdeep | 3072:ymIxNUlpIfw8SGopH8x+iHdoLqp6vif+zUD:ymIr4Ga8x7HdLp6vif+zUD | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| watch | Network communications indicative of a potential document or script payload download was initiated by the process excel.exe |
| watch | One or more non-whitelisted processes were created |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | File has been identified by 6 AntiVirus engines on VirusTotal as malicious |
| info | Checks amount of memory in system |
| info | One or more processes crashed |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|
Suricata ids
ET INFO TLS Handshake Failure
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)