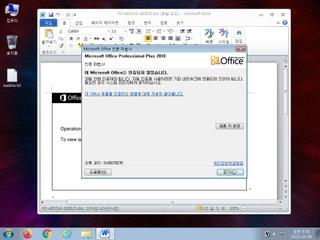
ScreenShot
| Created | 2023.03.09 10:01 | Machine | s1_win7_x6402 |
| Filename | PO-465514-180820.doc | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 47 detected (SAgent, malicious, high confidence, Emotet, Eldorado, GenScript, score, htfcpy, VBA@AI, Siggen2, AAGJ, Malware@#1nwenvpl4hdda, Detected, S1072, ai score=100, Static AI, Malicious OLE) | ||
| md5 | d7e6921bfd008f707ba52dee374ff3db | ||
| sha256 | 044aa7e93ec81b297b53aaebad9bbac1a9d754219b001aaf5d4261665af30bc7 | ||
| ssdeep | 3072:fNw4PrXcuQuvpzm4bkiaMQgAlSKQg0g3Vwse:bDRv1m4bnQgISKQg0gFwse | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 47 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| info | One or more processes crashed |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |
Network (13cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)