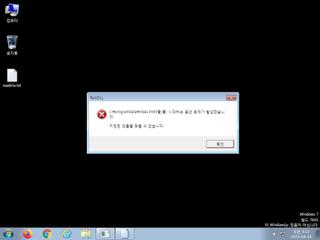
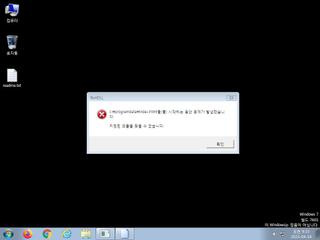
ScreenShot
| Created | 2023.04.19 09:37 | Machine | s1_win7_x6401 |
| Filename | Funds_792120.wsf | ||
| Type | UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | dbf85f39dd98463b298f50302d64ea40 | ||
| sha256 | 13bde59e20034a2ce1797c7890cdd770fedef78f29f0e47c558c6eb9d91e8f10 | ||
| ssdeep | 1536:uA8ZOy2JyfnK/32SNnW7s8LnNVcKOAuWQwnn5QJp985ElDCCjIWp:uQNJWnK/mSN58LnNVcg75Q186lDCji | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| danger | A potential heapspray has been detected. 4352 megabytes was sprayed onto the heap of the wscript.exe process |
| danger | The process wscript.exe wrote an executable file to disk which it then attempted to execute |
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | Communicates with host for which no DNS query was performed |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process wscript.exe |
| watch | One or more non-whitelisted processes were created |
| watch | Wscript.exe initiated network communications indicative of a script based payload download |
| watch | wscript.exe-based dropper (JScript |
| notice | Performs some HTTP requests |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|
Network (5cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)