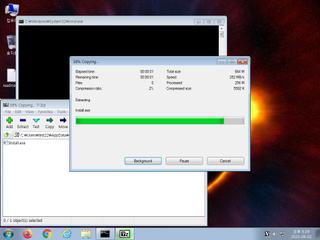
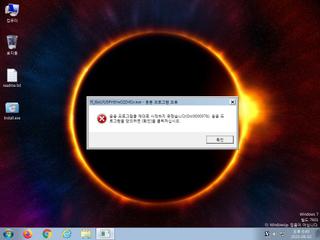
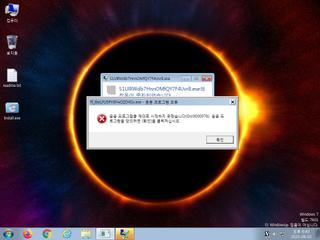
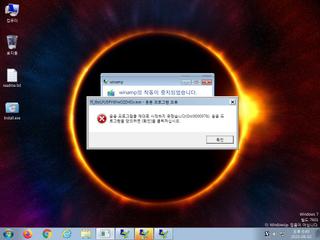
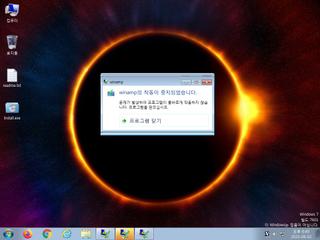
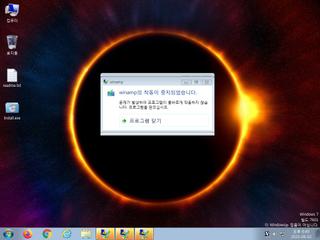
ScreenShot
| Created | 2023.06.02 18:43 | Machine | s1_win7_x6402 |
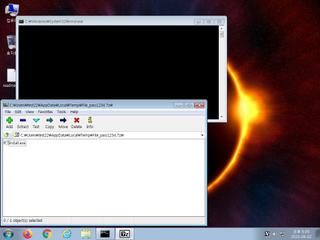
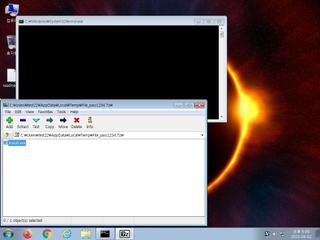
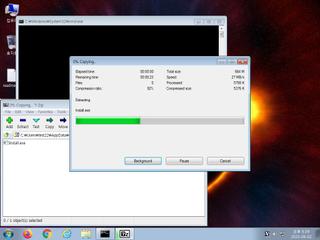
| Filename | File_pass1234.7z | ||
| Type | 7-zip archive data, version 0.4 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 63e2ad5f5f1466a924b0c77048dcc60a | ||
| sha256 | 23fb85714c79c4acf328e379128025ee17eca8f57d8a58d47da6d821d5f70737 | ||
| ssdeep | 98304:fg7CCMx7RpUpyVLUNqeTZTgl4PAzIrjfs8LRfmxKf0cmHs8nL7PmX4G7N:feex7RpDUNNTZtIMrjfBxq2TmHs8nfPM | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (15cnts)
| Level | Description |
|---|---|
| danger | Connects to IP addresses that are no longer responding to requests (legitimate services will remain up-and-running usually) |
| warning | Generates some ICMP traffic |
| watch | Communicates with host for which no DNS query was performed |
| watch | Connects to an IRC server |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Looks up the external IP address |
| notice | Performs some HTTP requests |
| notice | Resolves a suspicious Top Level Domain (TLD) |
| notice | Sends data using the HTTP POST Method |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (54cnts) ?
Suricata ids
ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
SURICATA Applayer Mismatch protocol both directions
ET MALWARE Win32/BeamWinHTTP CnC Activity M2 (GET)
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Download from dotted-quad Host
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO Packed Executable Download
ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging)
ET MALWARE RedLine Stealer TCP CnC net.tcp Init
ET MALWARE Redline Stealer TCP CnC Activity
ET MALWARE Redline Stealer TCP CnC - Id1Response
ET INFO TLS Handshake Failure
ET POLICY IP Check Domain (iplogger .org in TLS SNI)
ET MALWARE Amadey CnC Check-In
ET MALWARE Win32/Amadey Bot Activity (POST) M2
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET POLICY IP Check Domain (iplogger .org in DNS Lookup)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
SURICATA Applayer Mismatch protocol both directions
ET MALWARE Win32/BeamWinHTTP CnC Activity M2 (GET)
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Download from dotted-quad Host
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO Packed Executable Download
ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging)
ET MALWARE RedLine Stealer TCP CnC net.tcp Init
ET MALWARE Redline Stealer TCP CnC Activity
ET MALWARE Redline Stealer TCP CnC - Id1Response
ET INFO TLS Handshake Failure
ET POLICY IP Check Domain (iplogger .org in TLS SNI)
ET MALWARE Amadey CnC Check-In
ET MALWARE Win32/Amadey Bot Activity (POST) M2
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET POLICY IP Check Domain (iplogger .org in DNS Lookup)