ScreenShot
| Created | 2023.06.05 15:36 | Machine | s1_win7_x6402 |
| Filename | 51216324738.pdf | ||
| Type | PDF document, version 1.4 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 30 detected (Phishing, Spam, Phish, Save, Camelot, PhishingX, Malicious, score, Gen2, Phisher, Detected, Malurl, ai score=82, CLASSIC, Static AI, Malicious PDF) | ||
| md5 | e44cdb9b41b9e644d0a7366029ae9ec0 | ||
| sha256 | 662c3ebc15ce27480cd232e7af324b5a76f316c3416190452a4f62222da46762 | ||
| ssdeep | 3072:wC+roBABDeHh+GZfWW5sw6NbJ2PUJni/LvPPBL:w7K0o5sw6/6/zx | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 30 AntiVirus engines on VirusTotal as malicious |
| watch | Communicates with host for which no DNS query was performed |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
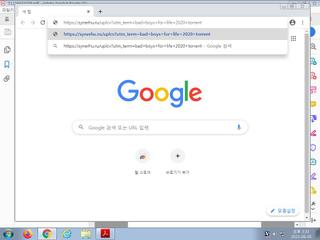
| notice | Performs some HTTP requests |
| notice | Resolves a suspicious Top Level Domain (TLD) |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
Rules (13cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | PDF_Suspicious_Link_Z | PDF Suspicious Link | binaries (upload) |
| notice | PDF_Format_Z | PDF Format | binaries (upload) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (23cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)