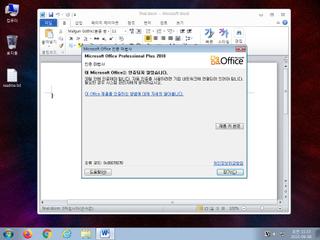
ScreenShot
| Created | 2023.06.08 11:15 | Machine | s1_win7_x6402 |
| Filename | final.docm | ||
| Type | Microsoft Word 2007+ | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 37 detected (malicious, high confidence, Valyria, Save, Eldorado, gen178, Kryptik, score, clxgqd, modification of W97M, Static AI, Malicious OPENXML, Donoff, Detected, S1222, ai score=88, CLASSIC) | ||
| md5 | ea8f8a4cd85177248a08490f05d1b555 | ||
| sha256 | 59e66b35a8f15c6803d1d0ea8fb77402a2e0f94b6fcdb6293c2256d2239d5afb | ||
| ssdeep | 384:/iutP+ns0xuhZNGkZKPXCCRNxt/ZtNNaZVC9WObKo1nofI:/XPIsgmGkMJjxllNaW7bKo10I | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (7cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| danger | File has been identified by 37 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| info | One or more processes crashed |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| info | docx | Word 2007 file format detection | binaries (upload) |
| info | zip_file_format | ZIP file format | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|