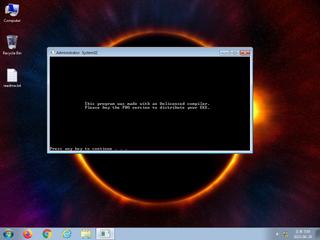
ScreenShot
| Created | 2023.06.29 17:08 | Machine | s1_win7_x6403 |
| Filename | postmonn.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 41 detected (MulDrop20, MSILZilla, Save, malicious, confidence, 100%, ZemsilF, xm0@aKjV@Yb, Eldorado, Attribute, HighConfidence, high confidence, score, Dapato, PWSX, high, AsyncRat, ABJU, Detected, ai score=83, unsafe, MSIL@AI, MSIL2, UY+uln4R3IJxA6Ig8NJR8w, Static AI, Malicious PE, susgen, Zilla) | ||
| md5 | d699bb26d34ae6d55afdbf3cec0174e3 | ||
| sha256 | 4e13c9a092b38e7add44ab18fbebc0f6b891d08a4a5d8c17d1fd194e574769b8 | ||
| ssdeep | 6144:vmTWCHJmBPFWYHdbfjg2Xf9w+ScZWCzYjPvQK2DiA5ePE46guHrUECMCSgZRBWjq:vrzB8ob7gqf9FIx7Q3DluhVSYOta+pS | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (24cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 41 AntiVirus engines on VirusTotal as malicious |
| watch | Communicates with host for which no DNS query was performed |
| watch | Creates an Alternate Data Stream (ADS) |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process powershell.exe |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Poweshell is sending data to a remote host |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | URL downloaded by powershell script |
| notice | Uses Windows utilities for basic Windows functionality |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Command line console output was observed |
| info | Powershell script has download & invoke calls |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (13cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PowerShell | PowerShell script | scripts |
| info | PowershellDI | Extract Download/Invoke calls from powershell script | scripts |
Suricata ids
SURICATA TLS invalid record type
SURICATA TLS invalid record/traffic
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
SURICATA TLS invalid record/traffic
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none