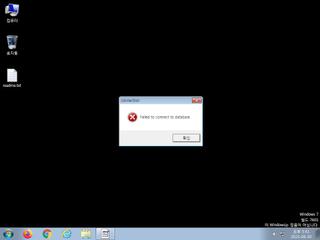
ScreenShot
| Created | 2023.06.30 17:46 | Machine | s1_win7_x6401 |
| Filename | knm.exe | ||
| Type | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 30 detected (malicious, high confidence, Tedy, V06z, Kryptik, AGen, Attribute, HighConfidence, score, Noon, MSILHeracles, PWSX, Artemis, Static AI, Suspicious PE, qkmii, ai score=85, Sabsik, Fsysna, irpn, unsafe, Chgt, MSIL@AI, MSIL2, kK3kllCpd1KCy, NOOyvD3Q, confidence, 100%) | ||
| md5 | b0011be8c7cd1c9865e1f1ed406197d4 | ||
| sha256 | 33e6b8a634ba08facba420eed6f61933570fb26e59fdba5a52603148c31e8792 | ||
| ssdeep | 192:VqwFkb7H0rKTW2eOF93JceyCxk6XY5V87W1tf8UoupfJf6myRRW3ZDkmiPmiz10:BUTcOF7cDUk6XYSswunHhITG | ||
| imphash | |||
| impfuzzy | 3:: | ||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 30 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | One or more processes crashed |
| info | This executable has a PDB path |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) is none
EAT(Export Address Table) is none
EAT(Export Address Table) is none