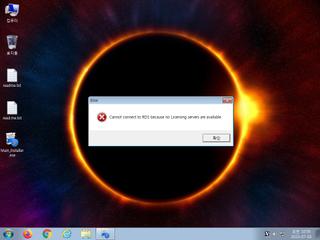
ScreenShot
| Created | 2023.07.03 11:00 | Machine | s1_win7_x6402 |
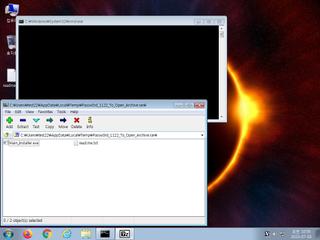
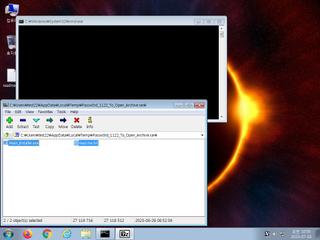
| Filename | Passw0rd_1122_To_Open_Archive.rar | ||
| Type | RAR archive data, v5 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | |||
| md5 | 2b3d3bcf435c1400b8a85945d6fe2d15 | ||
| sha256 | 2665c55ee0796f4954a237dc213e413dd961fd43821a40f7df5674c9a33e2e47 | ||
| ssdeep | 393216:yEGw1XQPLZdF/QblgMwU0zgLgeswpECSISff/GOyIAaR5xVqAi:yE3yZdF/0PwU0zSgyFi/8I75xVqAi | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Sends data using the HTTP POST Method |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (14cnts) ?
Suricata ids
ET INFO Executable Download from dotted-quad Host
ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile
ET MALWARE Win32/RecordBreaker CnC Checkin M1
ET MALWARE Win32/RecordBreaker CnC Checkin - Server Response
ET INFO Dotted Quad Host DLL Request
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET POLICY PE EXE or DLL Windows file download HTTP
ET MALWARE Generic .bin download from Dotted Quad
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET HUNTING Possible Generic Stealer Sending System Information
ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile
ET MALWARE Win32/RecordBreaker CnC Checkin M1
ET MALWARE Win32/RecordBreaker CnC Checkin - Server Response
ET INFO Dotted Quad Host DLL Request
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET POLICY PE EXE or DLL Windows file download HTTP
ET MALWARE Generic .bin download from Dotted Quad
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET HUNTING Possible Generic Stealer Sending System Information