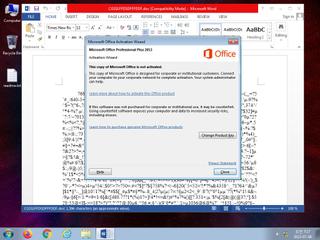
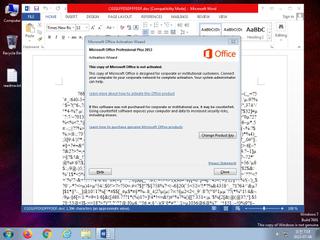
ScreenShot
| Created | 2023.07.06 07:24 | Machine | s1_win7_x6403 |
| Filename | CGSS1FFDSDFFFDDF.doc | ||
| Type | ISO-8859 text, with very long lines, with CR, LF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | |||
| md5 | 3483e943d6094354b09c224b748a3f4b | ||
| sha256 | f8b33ff580ced13d465ef0c495f9a649b6613b50e67d5083dcf385535e2c8a7e | ||
| ssdeep | 384:5o0zz3CcOrshtLcFj1fGQTvixosRgpfTBbGjRQ/K8crrnJqvKFwY5Z7sC:tzDTOY8JtJTvixosRgp79l+r085Z4C | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| info | One or more processes crashed |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | MS_RTF_Suspicious_documents | Suspicious documents using RTF document OLE object | binaries (upload) |
| warning | SUSP_INDICATOR_RTF_MalVer_Objects | Detects RTF documents with non-standard version and embedding one of the object mostly observed in exploit (e.g. CVE-2017-11882) documents. | binaries (upload) |
| info | Rich_Text_Format_Zero | Rich Text Format Signature Zero | binaries (upload) |