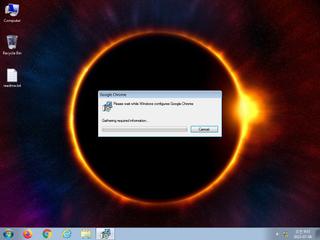
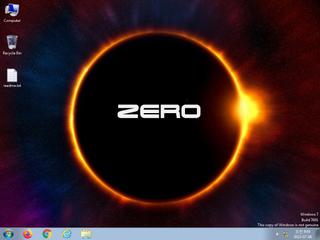
ScreenShot
| Created | 2023.07.06 09:06 | Machine | s1_win7_x6403_us |
| Filename | data.msi | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code p | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 25 detected (Lazy, ABRisk, JGXJ, Kryptik, HTMF, Malicious, score, Heavy, Qcnw, GenInflated, Artemis, nywxt, ai score=87, SwollenFile, CLASSIC) | ||
| md5 | 15f8410481816c5d95d8552728955ea1 | ||
| sha256 | f8ddcafbfee1e5c757514f1847f7ccda030f30f4e43b7b90a49242ed73d08678 | ||
| ssdeep | 49152:RpdSW7yOqvebAvGfW4u8sFgxnoWAlZvrDUE7A6:RpzyOqvZGiGoRvvUB6 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (7cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 25 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| info | CAB_file_format | CAB archive file | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|