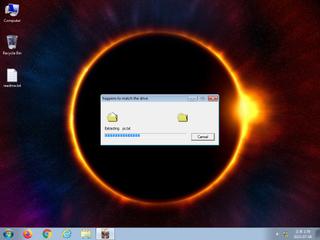
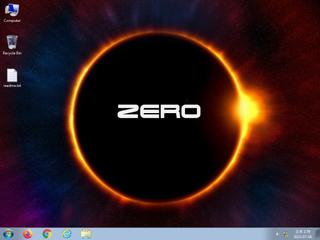
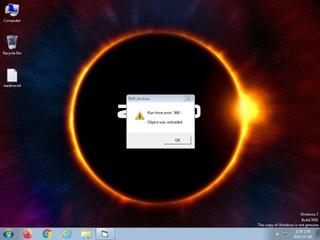
ScreenShot
| Created | 2023.07.08 14:07 | Machine | s1_win7_x6403 |
| Filename | Aas.EXE | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | |||
| VT API (file) | 22 detected (AIDetectMalware, Artemis, Vxo4, malicious, Kryptik, Eldorado, high confidence, multiple detections, high, score, SGeneric, Detected, BScope, Wacatac, unsafe, CLOUD, Behavior, confidence) | ||
| md5 | c3baac987bee5800b92b7e2d6d42db1a | ||
| sha256 | c6d4d7017e73509ff2023cbe9420d933868afa169eb47aa89711fc758bd9fd18 | ||
| ssdeep | 24576:NBNlNZ6OLlgJA60l+dgrRUiZY1dpjYjHZBzAUajpRBr46oIiVhX:zNlNZ6cgJA5ag46j5BzgZ5CX | ||
| imphash | 0ebb3c09b06b1666d307952e824c8697 | ||
| impfuzzy | 48:4bE7ob08sOaDm19a1SoV8KtsbW5KQ9Udwt8tGTE+Xl54LpNRoACu6x9KEVSvrza3:WE0b08s/DsE1BV8Ktsb9mEvM | ||
Network IP location
Signature (20cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 22 AntiVirus engines on VirusTotal as malicious |
| watch | Deletes executed files from disk |
| watch | Executes one or more WMI queries |
| watch | Installs itself for autorun at Windows startup |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | Uses Windows utilities for basic Windows functionality |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The file contains an unknown PE resource name possibly indicative of a packer |
| info | This executable has a PDB path |
Rules (13cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Emotet_RL_Gen_Zero | Win32 Trojan Emotet | binaries (upload) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Suspicious_Obfuscation_Script_2 | Suspicious obfuscation script (e.g. executable files) | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) Library
ADVAPI32.dll
0x1001000 FreeSid
0x1001004 AllocateAndInitializeSid
0x1001008 EqualSid
0x100100c GetTokenInformation
0x1001010 OpenProcessToken
0x1001014 AdjustTokenPrivileges
0x1001018 LookupPrivilegeValueA
0x100101c RegCloseKey
0x1001020 RegDeleteValueA
0x1001024 RegOpenKeyExA
0x1001028 RegSetValueExA
0x100102c RegQueryValueExA
0x1001030 RegCreateKeyExA
0x1001034 RegQueryInfoKeyA
KERNEL32.dll
0x100104c LocalFree
0x1001050 LocalAlloc
0x1001054 GetLastError
0x1001058 GetCurrentProcess
0x100105c lstrlenA
0x1001060 GetModuleFileNameA
0x1001064 GetSystemDirectoryA
0x1001068 _lclose
0x100106c _llseek
0x1001070 _lopen
0x1001074 WritePrivateProfileStringA
0x1001078 GetWindowsDirectoryA
0x100107c CreateDirectoryA
0x1001080 GetFileAttributesA
0x1001084 ExpandEnvironmentStringsA
0x1001088 lstrcpyA
0x100108c GlobalFree
0x1001090 GlobalUnlock
0x1001094 GlobalLock
0x1001098 GlobalAlloc
0x100109c IsDBCSLeadByte
0x10010a0 GetShortPathNameA
0x10010a4 GetPrivateProfileStringA
0x10010a8 GetPrivateProfileIntA
0x10010ac lstrcmpiA
0x10010b0 RemoveDirectoryA
0x10010b4 FindClose
0x10010b8 FindNextFileA
0x10010bc DeleteFileA
0x10010c0 SetFileAttributesA
0x10010c4 lstrcmpA
0x10010c8 FindFirstFileA
0x10010cc FreeResource
0x10010d0 GetProcAddress
0x10010d4 LoadResource
0x10010d8 SizeofResource
0x10010dc FindResourceA
0x10010e0 lstrcatA
0x10010e4 CloseHandle
0x10010e8 WriteFile
0x10010ec SetFilePointer
0x10010f0 SetFileTime
0x10010f4 LocalFileTimeToFileTime
0x10010f8 DosDateTimeToFileTime
0x10010fc SetCurrentDirectoryA
0x1001100 GetTempFileNameA
0x1001104 ExitProcess
0x1001108 CreateFileA
0x100110c LoadLibraryExA
0x1001110 lstrcpynA
0x1001114 GetVolumeInformationA
0x1001118 FormatMessageA
0x100111c GetCurrentDirectoryA
0x1001120 GetVersionExA
0x1001124 GetExitCodeProcess
0x1001128 WaitForSingleObject
0x100112c CreateProcessA
0x1001130 GetTempPathA
0x1001134 GetSystemInfo
0x1001138 CreateMutexA
0x100113c SetEvent
0x1001140 CreateEventA
0x1001144 CreateThread
0x1001148 ResetEvent
0x100114c TerminateThread
0x1001150 GetDriveTypeA
0x1001154 GetModuleHandleA
0x1001158 GetStartupInfoA
0x100115c GetCommandLineA
0x1001160 QueryPerformanceCounter
0x1001164 GetTickCount
0x1001168 GetCurrentThreadId
0x100116c GetCurrentProcessId
0x1001170 GetSystemTimeAsFileTime
0x1001174 TerminateProcess
0x1001178 UnhandledExceptionFilter
0x100117c SetUnhandledExceptionFilter
0x1001180 ReadFile
0x1001184 LoadLibraryA
0x1001188 GetDiskFreeSpaceA
0x100118c MulDiv
0x1001190 EnumResourceLanguagesA
0x1001194 FreeLibrary
0x1001198 LockResource
GDI32.dll
0x1001044 GetDeviceCaps
USER32.dll
0x10011a0 ExitWindowsEx
0x10011a4 wsprintfA
0x10011a8 CharNextA
0x10011ac CharUpperA
0x10011b0 CharPrevA
0x10011b4 SetWindowLongA
0x10011b8 GetWindowLongA
0x10011bc CallWindowProcA
0x10011c0 DispatchMessageA
0x10011c4 MsgWaitForMultipleObjects
0x10011c8 PeekMessageA
0x10011cc SendMessageA
0x10011d0 SetWindowPos
0x10011d4 ReleaseDC
0x10011d8 GetDC
0x10011dc GetWindowRect
0x10011e0 SendDlgItemMessageA
0x10011e4 GetDlgItem
0x10011e8 SetForegroundWindow
0x10011ec SetWindowTextA
0x10011f0 MessageBoxA
0x10011f4 DialogBoxIndirectParamA
0x10011f8 ShowWindow
0x10011fc EnableWindow
0x1001200 GetDlgItemTextA
0x1001204 EndDialog
0x1001208 GetDesktopWindow
0x100120c MessageBeep
0x1001210 SetDlgItemTextA
0x1001214 LoadStringA
0x1001218 GetSystemMetrics
COMCTL32.dll
0x100103c None
VERSION.dll
0x1001220 GetFileVersionInfoA
0x1001224 VerQueryValueA
0x1001228 GetFileVersionInfoSizeA
EAT(Export Address Table) is none
ADVAPI32.dll
0x1001000 FreeSid
0x1001004 AllocateAndInitializeSid
0x1001008 EqualSid
0x100100c GetTokenInformation
0x1001010 OpenProcessToken
0x1001014 AdjustTokenPrivileges
0x1001018 LookupPrivilegeValueA
0x100101c RegCloseKey
0x1001020 RegDeleteValueA
0x1001024 RegOpenKeyExA
0x1001028 RegSetValueExA
0x100102c RegQueryValueExA
0x1001030 RegCreateKeyExA
0x1001034 RegQueryInfoKeyA
KERNEL32.dll
0x100104c LocalFree
0x1001050 LocalAlloc
0x1001054 GetLastError
0x1001058 GetCurrentProcess
0x100105c lstrlenA
0x1001060 GetModuleFileNameA
0x1001064 GetSystemDirectoryA
0x1001068 _lclose
0x100106c _llseek
0x1001070 _lopen
0x1001074 WritePrivateProfileStringA
0x1001078 GetWindowsDirectoryA
0x100107c CreateDirectoryA
0x1001080 GetFileAttributesA
0x1001084 ExpandEnvironmentStringsA
0x1001088 lstrcpyA
0x100108c GlobalFree
0x1001090 GlobalUnlock
0x1001094 GlobalLock
0x1001098 GlobalAlloc
0x100109c IsDBCSLeadByte
0x10010a0 GetShortPathNameA
0x10010a4 GetPrivateProfileStringA
0x10010a8 GetPrivateProfileIntA
0x10010ac lstrcmpiA
0x10010b0 RemoveDirectoryA
0x10010b4 FindClose
0x10010b8 FindNextFileA
0x10010bc DeleteFileA
0x10010c0 SetFileAttributesA
0x10010c4 lstrcmpA
0x10010c8 FindFirstFileA
0x10010cc FreeResource
0x10010d0 GetProcAddress
0x10010d4 LoadResource
0x10010d8 SizeofResource
0x10010dc FindResourceA
0x10010e0 lstrcatA
0x10010e4 CloseHandle
0x10010e8 WriteFile
0x10010ec SetFilePointer
0x10010f0 SetFileTime
0x10010f4 LocalFileTimeToFileTime
0x10010f8 DosDateTimeToFileTime
0x10010fc SetCurrentDirectoryA
0x1001100 GetTempFileNameA
0x1001104 ExitProcess
0x1001108 CreateFileA
0x100110c LoadLibraryExA
0x1001110 lstrcpynA
0x1001114 GetVolumeInformationA
0x1001118 FormatMessageA
0x100111c GetCurrentDirectoryA
0x1001120 GetVersionExA
0x1001124 GetExitCodeProcess
0x1001128 WaitForSingleObject
0x100112c CreateProcessA
0x1001130 GetTempPathA
0x1001134 GetSystemInfo
0x1001138 CreateMutexA
0x100113c SetEvent
0x1001140 CreateEventA
0x1001144 CreateThread
0x1001148 ResetEvent
0x100114c TerminateThread
0x1001150 GetDriveTypeA
0x1001154 GetModuleHandleA
0x1001158 GetStartupInfoA
0x100115c GetCommandLineA
0x1001160 QueryPerformanceCounter
0x1001164 GetTickCount
0x1001168 GetCurrentThreadId
0x100116c GetCurrentProcessId
0x1001170 GetSystemTimeAsFileTime
0x1001174 TerminateProcess
0x1001178 UnhandledExceptionFilter
0x100117c SetUnhandledExceptionFilter
0x1001180 ReadFile
0x1001184 LoadLibraryA
0x1001188 GetDiskFreeSpaceA
0x100118c MulDiv
0x1001190 EnumResourceLanguagesA
0x1001194 FreeLibrary
0x1001198 LockResource
GDI32.dll
0x1001044 GetDeviceCaps
USER32.dll
0x10011a0 ExitWindowsEx
0x10011a4 wsprintfA
0x10011a8 CharNextA
0x10011ac CharUpperA
0x10011b0 CharPrevA
0x10011b4 SetWindowLongA
0x10011b8 GetWindowLongA
0x10011bc CallWindowProcA
0x10011c0 DispatchMessageA
0x10011c4 MsgWaitForMultipleObjects
0x10011c8 PeekMessageA
0x10011cc SendMessageA
0x10011d0 SetWindowPos
0x10011d4 ReleaseDC
0x10011d8 GetDC
0x10011dc GetWindowRect
0x10011e0 SendDlgItemMessageA
0x10011e4 GetDlgItem
0x10011e8 SetForegroundWindow
0x10011ec SetWindowTextA
0x10011f0 MessageBoxA
0x10011f4 DialogBoxIndirectParamA
0x10011f8 ShowWindow
0x10011fc EnableWindow
0x1001200 GetDlgItemTextA
0x1001204 EndDialog
0x1001208 GetDesktopWindow
0x100120c MessageBeep
0x1001210 SetDlgItemTextA
0x1001214 LoadStringA
0x1001218 GetSystemMetrics
COMCTL32.dll
0x100103c None
VERSION.dll
0x1001220 GetFileVersionInfoA
0x1001224 VerQueryValueA
0x1001228 GetFileVersionInfoSizeA
EAT(Export Address Table) is none