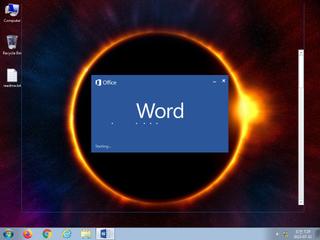
ScreenShot
| Created | 2023.07.11 07:33 | Machine | s1_win7_x6403 |
| Filename | templezx.doc | ||
| Type | Rich Text Format data, version 1, unknown character set | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | 33 detected (GenericKDZ, RTFObfustream, Save, CVE-2017-1188, Camelot, Malicious, score, dinbqn, Minerva, dihcb, Obfuscated, RTFMALFORM, RTFDl, Outbreak, AgentTesla, Detected, Malform, ai score=82, Probably Heur, RTFObfuscation, Rqil, AvsRicher, bZAyIk, CVE-2018-0798) | ||
| md5 | 96908698ef1a19e7b6c4cc2f52637d3b | ||
| sha256 | 798fa6d044ede82b78358f22b37053faad937fe49e84a0f98c7bd3f7e329d759 | ||
| ssdeep | 768:uFx0XaIsnPRIa4fwJMTzv5C4I3vn6C4foKmuG58BeGRGLuC:uf0Xvx3EMTjQj/Ko/uPrtC | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (7cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 33 AntiVirus engines on VirusTotal as malicious |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | RTF file has an unknown character set |
| info | One or more processes crashed |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | SUSP_INDICATOR_RTF_MalVer_Objects | Detects RTF documents with non-standard version and embedding one of the object mostly observed in exploit (e.g. CVE-2017-11882) documents. | binaries (upload) |
| info | Rich_Text_Format_Zero | Rich Text Format Signature Zero | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|