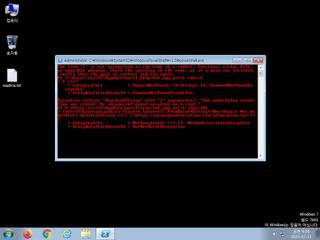
ScreenShot
| Created | 2023.07.11 09:38 | Machine | s1_win7_x6401 |
| Filename | bv6.jpg.ps1 | ||
| Type | ASCII text, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | 8f1d7cb8f3b9b72dd69fc451fca11a64 | ||
| sha256 | 44ea706bf0b7cf5679818eb129e6948ce9fb702de8d7dffa643eb5a4a2ead228 | ||
| ssdeep | 24:b5UBKC2qbQdmBKC2qb25V6Hpjs6HVx76Hnjs6Hoss6HrJs6HZ1VfSMnkFlmi:b5UB36dmB3cipKTLV5KMTi | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| watch | Network communications indicative of a potential document or script payload download was initiated by the process powershell.exe |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Poweshell is sending data to a remote host |
| notice | URL downloaded by powershell script |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |