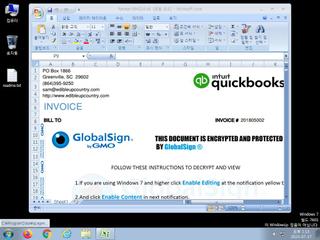
ScreenShot
| Created | 2023.07.17 13:14 | Machine | s1_win7_x6401 |
| Filename | Receipt-894324.xls | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 37 detected (malicious, high confidence, Siggen3, Valyria, Eldorado, 0NA103GF21, MSHTA, Ole2, druvzi, MacroS, Malware@#lc7v1onpryii, ADXD, Static AI, Suspicious OLE, AJAM, ai score=99, Dridex, PSTT, score) | ||
| md5 | 73f2506109fae384bc40c7ba7cb5fc9c | ||
| sha256 | eb5b61b197c89ba6a19d3eaeda56d858f6bd30beaff0a43719fc5c6591e7ad2d | ||
| ssdeep | 12288:DRYbXrlUc6XS/CwRl+4MW1H5onZHBDznxcp/c0UGtkbByxlFYd2DrpE9Nr:sUc6EjDMW1UrDjxcNcfgZI2or | ||
| imphash | |||
| impfuzzy | |||
Network IP location
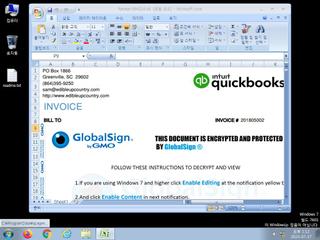
Signature (6cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 37 AntiVirus engines on VirusTotal as malicious |
| watch | Creates suspicious VBA object |
| watch | One or more non-whitelisted processes were created |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates a suspicious process |
| info | Checks amount of memory in system |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |