ScreenShot
| Created | 2023.07.19 09:16 | Machine | s1_win7_x6401 |
| Filename | Document_of_file_newshipment_pdf.js | ||
| Type | Little-endian UTF-16 Unicode text, with CRLF, CR line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 20 detected (Cryxos, Remcos, iacgm, ai score=89, Detected, PowerShell) | ||
| md5 | 5d13e163a153f92e5f656a1fd26269df | ||
| sha256 | 6f39593b4a9ba49a8ca212b7a5d77298542ad2bb2a369affae481ccf134ab91b | ||
| ssdeep | 48:oRpNA6vkeVl1DBcrOuf+vM9jrgnASH1+XI3VtegWQQ5VC9:o/66sOFf3OlC9 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (6cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 20 AntiVirus engines on VirusTotal as malicious |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process wscript.exe |
| watch | Wscript.exe initiated network communications indicative of a script based payload download |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Performs some HTTP requests |
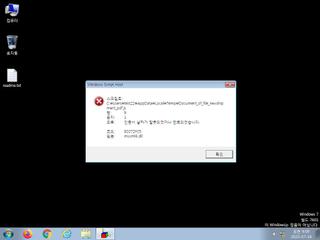
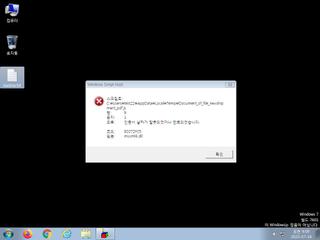
| info | One or more processes crashed |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|
Network (7cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET POLICY Observed DNS Query to Pastebin-style Service (wtools .io)
ET POLICY Observed DNS Query to Pastebin-style Service (wtools .io)