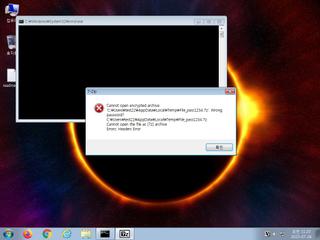
ScreenShot
| Created | 2023.07.26 11:23 | Machine | s1_win7_x6402 |
| Filename | File_pass1234.7z | ||
| Type | 7-zip archive data, version 0.4 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | |||
| md5 | dd48d433b225a68e26ca5b6446f0e5f9 | ||
| sha256 | d4627bbc66102d5e9c18b434de81a139c275ab4810e337e6a1f9f7cdf54a24ea | ||
| ssdeep | 98304:qMYYHZAjSqzkr6cFiKtSlqoQPNmNQ410Oo9jv:3ZAPcFinVNYj7 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|