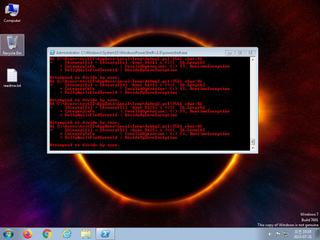
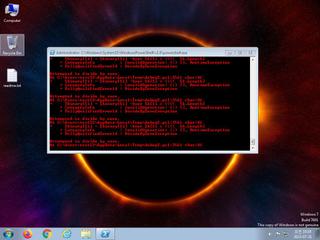
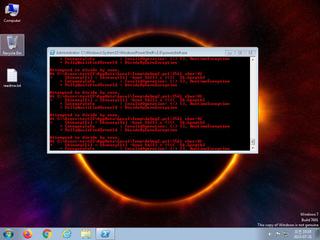
ScreenShot
| Created | 2023.07.31 10:23 | Machine | s1_win7_x6403 |
| Filename | debug2.ps1 | ||
| Type | ASCII text, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | |||
| md5 | 385c874a9adc94c9cddb7618a86b8299 | ||
| sha256 | fdbbad1514d6b72b95d3a21c4e365ac864c82dbedda219f570d7eaf61339d532 | ||
| ssdeep | 6144:3Hzv3Zq3Mmw90EHnlpoGMtWK646yjUF92JiWtDQAiEKwUaWg8h7Rntlr3OfTpe1K:3H8gh46SME2Sfs5YU8S2Ttb | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (13cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process powershell.exe |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Poweshell is sending data to a remote host |
| notice | URL downloaded by powershell script |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |