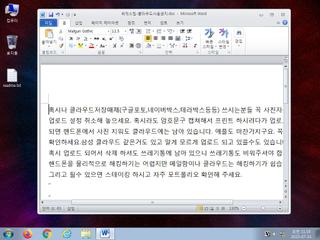
ScreenShot
| Created | 2023.07.31 11:20 | Machine | s1_win7_x6402 |
| Filename | 위믹스팀-클라우드사용금지.doc | ||
| Type | Microsoft Word 2007+ | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | 31 detected (malicious, high confidence, GenericKD, Eldorado, gen175, Kimsuky, score, Ole2, druvzi, CLASSIC, Artemis, 8D3DSM, W2000M, Minerva, fmbdg, Leonem, SLoad, Detected, ai score=80, MacroS, Static AI, Malicious OPENXML) | ||
| md5 | b6614471ebf288689d33808c376540e1 | ||
| sha256 | 928e61590b2c4acf3991bd4327c5107c1cfd2604d992647c4e63bd1d620ff636 | ||
| ssdeep | 384:/imtKoiaQnGaOF6YWS7xUpooaDTGDFDhfgZCEn0i13LXFCkR0iuK+fxE1ccCtk8:/LhiaQvOF6YN6Ta3GDUPv13R50iUfx3V | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 31 AntiVirus engines on VirusTotal as malicious |
| watch | A command shell or script process was created by an unexpected parent process |
| watch | One or more non-whitelisted processes were created |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| info | Command line console output was observed |
| info | One or more processes crashed |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| info | docx | Word 2007 file format detection | binaries (upload) |
| info | zip_file_format | ZIP file format | binaries (upload) |
| info | test_office | test url | scripts |