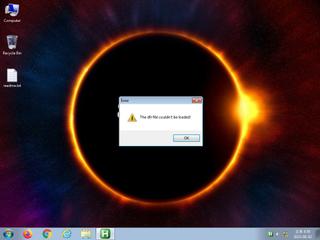
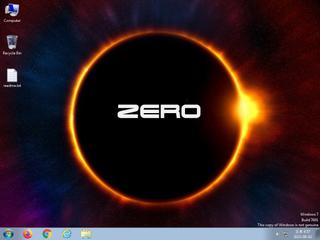
ScreenShot
| Created | 2023.08.02 17:04 | Machine | s1_win7_x6403 |
| Filename | x-admins.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 21 detected (AIDetectMalware, Artemis, Attribute, HighConfidence, malicious, moderate confidence, score, high, Static AI, Malicious PE, auxn, PossibleThreat, MUPX, Gen@24tbus, Phonzy, R325756, Generic@AI, RDML, AF2cKbJeSE3sCytm9DaVGA, susgen, confidence) | ||
| md5 | 1bdfa5d4db8f961fb85677c4d8bb64f4 | ||
| sha256 | 2e54ec22a0d7931509bb5905acf51ac1f223d5bca7a46b9f9038291d7c80c6c9 | ||
| ssdeep | 6144:ndkzF43SM5dCsenQjq2Zs4ogcAWUwxPk47oLFldV1jJrBBxRdE3ajPXoSI84KF:n6zF4vCT4q2Z7NBWrl7EzdH9BL5PXoSz | ||
| imphash | 604d14eda74ecb05dc3fd3f2233fd004 | ||
| impfuzzy | 6:omRgsyICeGaWvOYZBJAEoZ/OEGDzyRZr4BJTbBnaOAMyyTcf546PIIsLdJl0yn:omRgUoABZG/Dzgr4BJZLAITRIIIsLHlH | ||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 21 AntiVirus engines on VirusTotal as malicious |
| watch | Attempts to create or modify system certificates |
| watch | Creates a windows hook that monitors keyboard input (keylogger) |
| watch | Installs an hook procedure to monitor for mouse events |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Performs some HTTP requests |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | The executable is compressed using UPX |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (4cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) Library
ADVAPI32.dll
0x4d7644 RegCloseKey
COMCTL32.dll
0x4d764c None
COMDLG32.dll
0x4d7654 GetSaveFileNameA
GDI32.dll
0x4d765c BitBlt
KERNEL32.DLL
0x4d7664 LoadLibraryA
0x4d7668 ExitProcess
0x4d766c GetProcAddress
0x4d7670 VirtualProtect
ole32.dll
0x4d7678 CoGetObject
OLEAUT32.dll
0x4d7680 SysStringLen
PSAPI.DLL
0x4d7688 GetModuleBaseNameA
SHELL32.dll
0x4d7690 DragFinish
USER32.dll
0x4d7698 GetDC
VERSION.dll
0x4d76a0 VerQueryValueA
WININET.dll
0x4d76a8 InternetOpenA
WINMM.dll
0x4d76b0 mixerOpen
WSOCK32.dll
0x4d76b8 WSAStartup
EAT(Export Address Table) is none
ADVAPI32.dll
0x4d7644 RegCloseKey
COMCTL32.dll
0x4d764c None
COMDLG32.dll
0x4d7654 GetSaveFileNameA
GDI32.dll
0x4d765c BitBlt
KERNEL32.DLL
0x4d7664 LoadLibraryA
0x4d7668 ExitProcess
0x4d766c GetProcAddress
0x4d7670 VirtualProtect
ole32.dll
0x4d7678 CoGetObject
OLEAUT32.dll
0x4d7680 SysStringLen
PSAPI.DLL
0x4d7688 GetModuleBaseNameA
SHELL32.dll
0x4d7690 DragFinish
USER32.dll
0x4d7698 GetDC
VERSION.dll
0x4d76a0 VerQueryValueA
WININET.dll
0x4d76a8 InternetOpenA
WINMM.dll
0x4d76b0 mixerOpen
WSOCK32.dll
0x4d76b8 WSAStartup
EAT(Export Address Table) is none