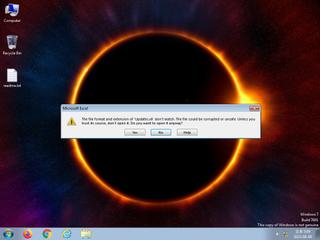
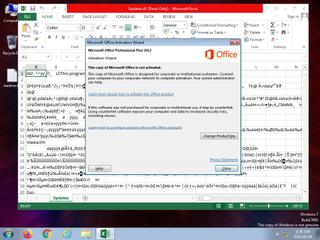
ScreenShot
| Created | 2023.08.09 17:15 | Machine | s1_win7_x6403 |
| Filename | loader.hta | ||
| Type | HTML document, ASCII text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | 4 detected (Obfuscated, ExpKit, fbenub, Kakash) | ||
| md5 | 2c3231b88b767d7d01eefbd05868b3a8 | ||
| sha256 | 90f54fa2d59842359840b4dff68127bfe0a1f34fe88c0079fe516c9119ffc90d | ||
| ssdeep | 24576:zNAAb8qgTiiPJQ7ATsutd+6ZTE814Az4wm8fzBXokSGikMaLch3RGW1a37D:BymqS7AW8TEzcFSlDhRJ8 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (15cnts)
| Level | Description |
|---|---|
| watch | Harvests credentials from local email clients |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | File has been identified by 4 AntiVirus engines on VirusTotal as malicious |
| notice | Queries for potentially installed applications |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | One or more processes crashed |
| info | Tries to locate where the browsers are installed |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (22cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| warning | hide_executable_file | Hide executable file | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE64 | (no description) | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|