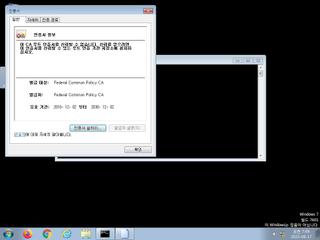
ScreenShot
| Created | 2023.08.17 07:50 | Machine | s1_win7_x6401 |
| Filename | Federal Common Policy CA.cer | ||
| Type | data | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 8c42b6360dd024ce4cb1ba06d26a6bc9 | ||
| sha256 | 894ebc0b23da2a50c0186b7f8f25ef1f6b2935af32a94584ef80aaf877a3a06e | ||
| ssdeep | 24:9d9cIXSd9cIL7ob7DwYO1p9WFLj+TeAdLfIS5xp5Xk0AxRwIqhbXK:/vXKv3I7NOJaj+BQm5SRqd6 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Yara rule detected in process memory |
| info | Checks if process is being debugged by a debugger |
Rules (8cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|