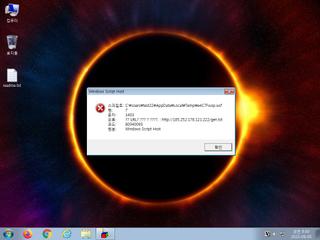
ScreenShot
| Created | 2023.09.05 08:43 | Machine | s1_win7_x6402 |
| Filename | e4C7Fwop.wsf | ||
| Type | UTF-8 Unicode text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 6f83b9c7c240127c0b92ce814d02bcb0 | ||
| sha256 | 9bdac91cec897f3b2fdb8ecd1fd279cdfa708ef5629d8f090d66fa96a2d8468a | ||
| ssdeep | 384:xp5ocorp5ocorp5ocorp5ocorp5ocorp5ocorp5ocorp5ocorp5ocorp5ocorp5u:J+d | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | Communicates with host for which no DNS query was performed |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process wscript.exe |
| watch | Wscript.exe initiated network communications indicative of a script based payload download |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|