ScreenShot
| Created | 2023.09.07 17:45 | Machine | s1_win7_x6403 |
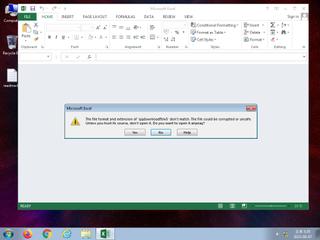
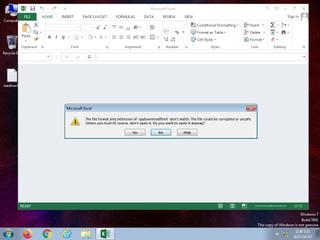
| Filename | qqdownloadftnv5 | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 936, Autho | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 45 detected (Kagatang, malicious, high confidence, Save, Laroux, Escoper, score, EMOTET, YXCDFZ, ExcelSic, fkbqor, OLE2, Static AI, Malicious OLE, Kangatang, Detected, ai score=85, CLASSIC, Valyria) | ||
| md5 | 9cbc21a9ed6e1525332557904760e570 | ||
| sha256 | d01d9b66eafe89da8b1b3cb45b194dc7d770c55bcabfb752c13f2b835b864f05 | ||
| ssdeep | 6144:6bVflDcacWc6oRaHUNJUPG1o98Bjr6PRBy9SY9bNtdbwtm8shKW4Idf9t8qre04I:Wqre04CDiWmi7DPoCR71 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (6cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 45 AntiVirus engines on VirusTotal as malicious |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Yara rule detected in process memory |
Rules (16cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
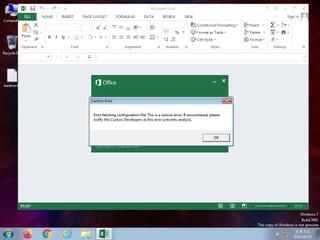
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|