ScreenShot
| Created | 2023.09.14 14:33 | Machine | s1_win7_x6401 |
| Filename | convert-pdf-591.js | ||
| Type | ASCII text | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 44096c929ae4aa847f13d91311eb84b8 | ||
| sha256 | f56295432ae84c8b1b48024edae29939ae8d0ff988b97ba77169343d6ada72f3 | ||
| ssdeep | 384:D6sdEZ3d3+3S+dfOMGxKecfBVQjgvlzbzNYCAHNo1mB9yWbWyF7Xv99ndMzktipM:RdEL3fpP+nb1InhBQayb6Q3pu | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (13cnts)
| Level | Description |
|---|---|
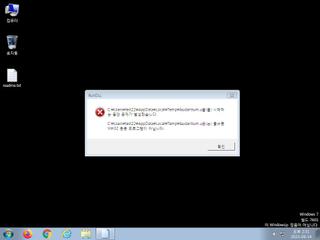
| danger | The process wscript.exe wrote an executable file to disk which it then attempted to execute |
| watch | Deletes executed files from disk |
| watch | Drops a binary and executes it |
| watch | One or more non-whitelisted processes were created |
| notice | A process created a hidden window |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | One or more potentially interesting buffers were extracted |
| notice | Starts servers listening |
| notice | Uses Windows utilities for basic Windows functionality |
| info | Command line console output was observed |
Rules (7cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |