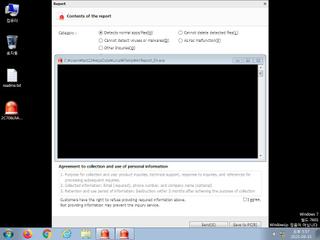
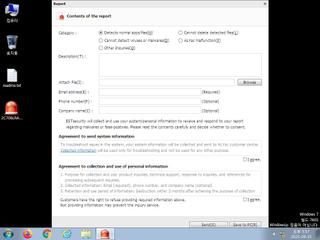
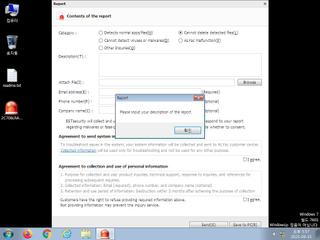
ScreenShot
| Created | 2023.09.15 18:00 | Machine | s1_win7_x6401 |
| Filename | AYReport_EN.exe | ||
| Type | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 47 detected (Binder, unsafe, Vja7, malicious, confidence, 100%, MsilDrop, Attribute, HighConfidence, high confidence, score, DropperX, Gen2, R002C0RIE23, Static AI, Malicious PE, twon, GH@60rvah, FormBook, Detected, Artemis, ai score=89, dGZlOgwTO, kFakrH0A, Outbreak, ZemsilF, @pW@aWtH8Rp) | ||
| md5 | ec333982af0977d8af5a4984792a4385 | ||
| sha256 | bde2b977cdd7c086a35825a9ba7f2307341a3917f40cc193ed316dde106a6c74 | ||
| ssdeep | 49152:LLLjKXCrX+hMesdq40bf95X9K5NRcSJDg/u/fiGhG6E7/6bp1pBt0zKkevwN/+jA: | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (14cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 47 AntiVirus engines on VirusTotal as malicious |
| watch | Detects Avast Antivirus through the presence of a library |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Queries for the computername |
Rules (15cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | PhysicalDrive_20181001 | (no description) | binaries (download) |
| watch | ASPack_Zero | ASPack packed file | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none