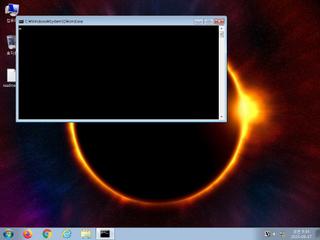
ScreenShot
| Created | 2023.09.17 09:38 | Machine | s1_win7_x6402 |
| Filename | Invoice_88737.lnk | ||
| Type | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has Working directory, Has command line arguments, Icon number=0, Archive, ctime=Fri May 7 23:16:08 2021, mtime=Fri May 7 23:16:08 2021, atime=Fri May 7 23:16: | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 5 detected (PSRunner, CLASSIC, Probably Heur, LNKScript, Static AI, Suspicious LNK) | ||
| md5 | 9226cdef332b7e61317d0d12e76578c8 | ||
| sha256 | 916ea8bc5735dae25ea4df4eadba0da4f85fdaeaf99dd6f7210e44ee594425e2 | ||
| ssdeep | 24:8FimDF69tYDvqswCK4IWsOmJBWkp+/CWRHUTHVHeEcR5FpYkUm:8smR69tGy4sjJ4m14R5FplU | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (22cnts)
| Level | Description |
|---|---|
| watch | A process performed obfuscation on information about the computer or sent it to a remote location indicative of CnC Traffic/Preperations. |
| watch | Communicates with host for which no DNS query was performed |
| watch | Creates a suspicious Powershell process |
| watch | Creates a windows hook that monitors keyboard input (keylogger) |
| watch | Drops a binary and executes it |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | The process powershell.exe wrote an executable file to disk |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | File has been identified by 5 AntiVirus engines on VirusTotal as malicious |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (18cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsPE64 | (no description) | binaries (download) |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (upload) |
| info | Lnk_Format_Zero | LNK Format | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (6cnts) ?
Suricata ids
ET INFO Dotted Quad Host VBS Request
ET INFO Dotted Quad Host ZIP Request
ET INFO Executable Download from dotted-quad Host
ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile
ET HUNTING WebDAV Retrieving .exe
ET INFO Dotted Quad Host ZIP Request
ET INFO Executable Download from dotted-quad Host
ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile
ET HUNTING WebDAV Retrieving .exe