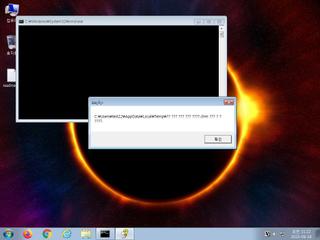
ScreenShot
| Created | 2023.09.18 11:25 | Machine | s1_win7_x6402 |
| Filename | 북의 핵위협 양상과 한국의 대응방향.chm | ||
| Type | MS Windows HtmlHelp Data | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 16 detected (Save, ai score=86, MouseJack, CLASSIC) | ||
| md5 | 364d4fdf430477222fe854b3cd5b6d40 | ||
| sha256 | c62677543eeb50e0def44fc75009a7748cdbedd0a3ccf62f50d7f219f6a5aa05 | ||
| ssdeep | 768:5UU18TPTd1QC2NQeaOcm/4hdY/kdJLyltH:5UUCTPT7QtQ7m/4h40ultH | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (6cnts)
| Level | Description |
|---|---|
| watch | File has been identified by 16 AntiVirus engines on VirusTotal as malicious |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | One or more processes crashed |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | anti_dbg | Checks if being debugged | memory |
| info | chm_file_format | chm file format | binaries (upload) |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|