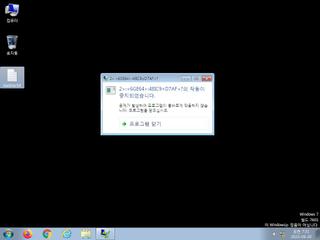
ScreenShot
| Created | 2023.09.20 07:34 | Machine | s1_win7_x6401 |
| Filename | test.exe | ||
| Type | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 26 detected (AIDetectMalware, malicious, high confidence, Artemis, Vx9w, Attribute, HighConfidence, Kryptik, AJRH, score, TrojanX, CoinMiner, moderate, Generic Reputation PUA, Znyonm, Chgt, SMOKELOADER, YXDITZ, Static AI, Suspicious PE, GenericKD, confidence, 100%) | ||
| md5 | 8dc615a726d1e47c1bbda80d36de8eb4 | ||
| sha256 | e00aa3c4c4c619fc05fc7deec32ca06959076b3df1063fd2da4205cca4882a94 | ||
| ssdeep | 24576:2vHqUf9Dd9r4YHM8XoWHeGabsKgQImgP07Bj3jGjAq/nWJrD+Z3pZiYCcQC+efTg:aqUf9Dd9r4YHM8XoWHeGabsKgQIm+o3B | ||
| imphash | |||
| impfuzzy | 3:: | ||
Network IP location
Signature (1cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 26 AntiVirus engines on VirusTotal as malicious |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) is none
EAT(Export Address Table) is none
EAT(Export Address Table) is none