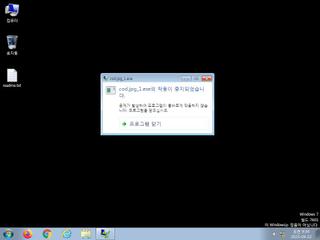
ScreenShot
| Created | 2023.09.22 09:36 | Machine | s1_win7_x6401 |
| Filename | cod.jpg_1.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 66f08e67109b6c6f161530d6f2e009d2 | ||
| sha256 | 792eed673f4c61948715751194f873bb80a837ce8efb4359fd537b8d7eb16421 | ||
| ssdeep | 1536:o2wukvF1ak9gcKu5UYFqY+jT4yXXUbrmtnE4nvtrQTGVx:o2dkvF1ak9Ku5UYFq7P4dbrmCAGex | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (0cnts)
| Level | Description |
|---|
Rules (8cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | AsyncRat | AsyncRat Payload | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (upload) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Suricata ids
ET INFO DYNAMIC_DNS Query to a *.ddnsfree .com Domain
ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server)
ET MALWARE Generic AsyncRAT Style SSL Cert
ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server)
ET MALWARE Generic AsyncRAT Style SSL Cert
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none