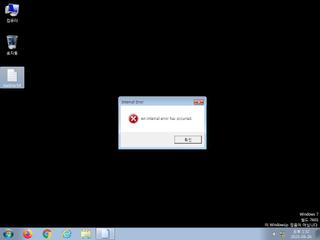
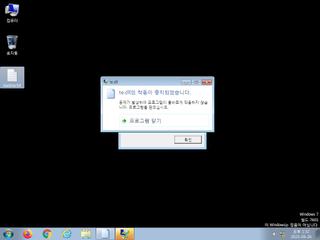
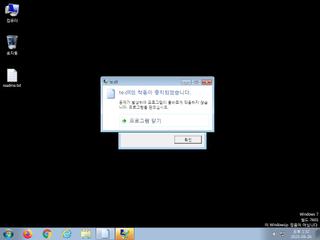
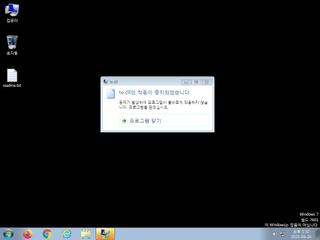
ScreenShot
| Created | 2023.09.26 13:36 | Machine | s1_win7_x6401 |
| Filename | te | ||
| Type | PE32+ executable (DLL) (GUI) x86-64 (stripped to external PDB), for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | |||
| md5 | 0c55abf72ac32c1f4364d2beacbc4eb6 | ||
| sha256 | 1cf703acb22aea9590903101ee616576d07504b491954146da618ef3954bb6a5 | ||
| ssdeep | 192:IU5z9i9veq2pJk+/qcJklyJOEtQF08TjsvGQwrgAhp:9z9SvWJH/IwJOUQF08UeQwrgC | ||
| imphash | fd410436ce0407a0a8f79bfce8af0bc3 | ||
| impfuzzy | 6:9mRxybmRxn5X0ZRHmRxT7mRx8Jt0yRlbmARrKXVNIV5GGaJvuqBYq0IquZzwD3:YRJRJJoARZqRNqBrKlaRa91Kq0iZzwD3 | ||
Network IP location
Signature (12cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a suspicious process |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | One or more processes crashed |
Rules (15cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsDLL | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x1f6969128 DeleteCriticalSection
0x1f6969130 EnterCriticalSection
0x1f6969138 GetLastError
0x1f6969140 InitializeCriticalSection
0x1f6969148 LeaveCriticalSection
0x1f6969150 Sleep
0x1f6969158 TlsGetValue
0x1f6969160 VirtualProtect
0x1f6969168 VirtualQuery
0x1f6969170 WinExec
msvcrt.dll
0x1f6969180 __iob_func
0x1f6969188 _amsg_exit
0x1f6969190 _initterm
0x1f6969198 _lock
0x1f69691a0 _unlock
0x1f69691a8 abort
0x1f69691b0 calloc
0x1f69691b8 free
0x1f69691c0 fwrite
0x1f69691c8 realloc
0x1f69691d0 strlen
0x1f69691d8 strncmp
0x1f69691e0 vfprintf
USER32.dll
0x1f69691f0 MessageBoxA
EAT(Export Address Table) Library
0x1f6963000 hash
0x1f69613a0 reverseString
0x1f69613f0 xlAutoOpen
KERNEL32.dll
0x1f6969128 DeleteCriticalSection
0x1f6969130 EnterCriticalSection
0x1f6969138 GetLastError
0x1f6969140 InitializeCriticalSection
0x1f6969148 LeaveCriticalSection
0x1f6969150 Sleep
0x1f6969158 TlsGetValue
0x1f6969160 VirtualProtect
0x1f6969168 VirtualQuery
0x1f6969170 WinExec
msvcrt.dll
0x1f6969180 __iob_func
0x1f6969188 _amsg_exit
0x1f6969190 _initterm
0x1f6969198 _lock
0x1f69691a0 _unlock
0x1f69691a8 abort
0x1f69691b0 calloc
0x1f69691b8 free
0x1f69691c0 fwrite
0x1f69691c8 realloc
0x1f69691d0 strlen
0x1f69691d8 strncmp
0x1f69691e0 vfprintf
USER32.dll
0x1f69691f0 MessageBoxA
EAT(Export Address Table) Library
0x1f6963000 hash
0x1f69613a0 reverseString
0x1f69613f0 xlAutoOpen