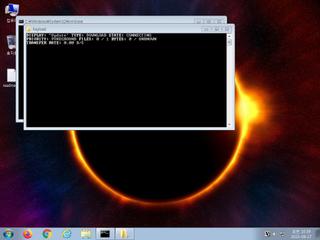
ScreenShot
| Created | 2023.09.27 10:41 | Machine | s1_win7_x6402 |
| Filename | Payload.lnk | ||
| Type | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=4, Archive, ctime=Wed Oct 6 04:31:17 2021, mtime=Sat Sep 23 13:05:22 2023, atime=Wed Oct 6 04:31 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 30 detected (WinLNK, Bitsuh, Pantera, Bitsldr, Camelot, BitsAdmin, CLASSIC, LnkGen, LNKEXEC, DownLnk, Outbreak, many, Znyonm, Detected, FBRQ, ai score=80, Link, DoubleRun, Probably Heur, LNKScript, Qqil) | ||
| md5 | 43efb83e1d56e903d06ed74df2a5f859 | ||
| sha256 | 7829789bb0290ad34295531e1fb55c2bcedf839062fddd1ddaf98852ad5a5419 | ||
| ssdeep | 24:83kWJ3q3c/wT+MacqJM9BGPJ+/omxdd2sZDjWC4o085CwdRqaqNp1deOm:8Uc3DzcqJwG4msZDjW9ojRI1gO | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| danger | File has been identified by 30 AntiVirus engines on VirusTotal as malicious |
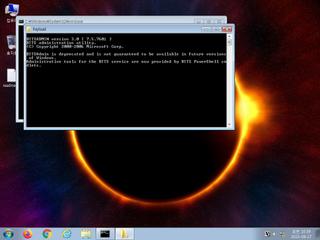
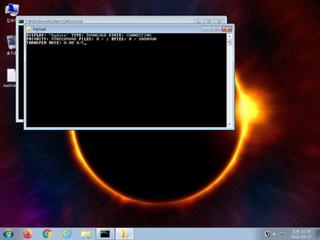
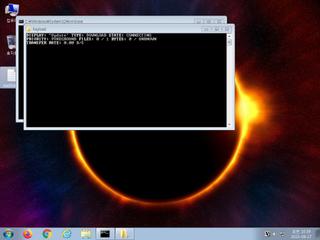
| watch | BITSAdmin Tool has been invoked to download a file |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | Uses suspicious command line tools or Windows utilities |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Yara rule detected in process memory |
| info | Command line console output was observed |
Rules (12cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (upload) |
| info | Lnk_Format_Zero | LNK Format | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |