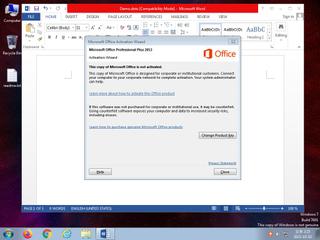
ScreenShot
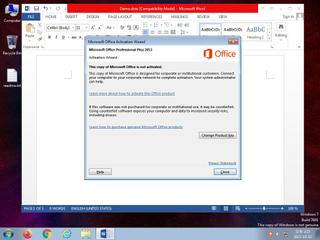
| Created | 2023.10.02 14:27 | Machine | s1_win7_x6403 |
| Filename | Demo.dotx | ||
| Type | Microsoft Word 2007+ | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 1584bacd2e30ac9f584eb9cf8f843312 | ||
| sha256 | dbb76f0c54100889190b0fef84c803b27bf604dd0b363921a64b82ef39fc6102 | ||
| ssdeep | 192:sztObzj89/6uyMtWNY6cDoWBmF0mqQTnhr5OG5VP0bFTB8GoA6a1n4N:itOkJyMti3cDoWBmXLONdR4N | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (14cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | One or more non-whitelisted processes were created |
| watch | Uses Sysinternals tools in order to add additional command line functionality |
| watch | Zeus P2P (Banking Trojan) |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates hidden or system file |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| info | Checks amount of memory in system |
| info | Collects information to fingerprint the system (MachineGuid |
| info | One or more processes crashed |
| info | Queries for the computername |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | docx | Word 2007 file format detection | binaries (upload) |
| info | zip_file_format | ZIP file format | binaries (upload) |
Network (6cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET POLICY Possible HTA Application Download
ET INFO Dotted Quad Host HTA Request
ET EXPLOIT SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl
ET EXPLOIT MSXMLHTTP Download of HTA (Observed in CVE-2017-0199)
ET WEB_CLIENT Office Requesting .HTA File Likely CVE-2017-0199 Request
ET USER_AGENTS Microsoft Office Existence Discovery User-Agent
ET WEB_CLIENT Office Discovery HTA file Likely CVE-2017-0199 Request M2
ET POLICY Possible HTA Application Download
ET INFO Dotted Quad Host HTA Request
ET EXPLOIT SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl
ET EXPLOIT MSXMLHTTP Download of HTA (Observed in CVE-2017-0199)
ET WEB_CLIENT Office Requesting .HTA File Likely CVE-2017-0199 Request
ET USER_AGENTS Microsoft Office Existence Discovery User-Agent
ET WEB_CLIENT Office Discovery HTA file Likely CVE-2017-0199 Request M2