ScreenShot
| Created | 2023.10.03 19:49 | Machine | s1_win7_x6401 |
| Filename | UpdateSvc.exe | ||
| Type | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 53 detected (Mardom, malicious, high confidence, MSILMamut, Artemis, Payola, Vghu, Genus, ABRisk, UXGS, Filecoder, jymssw, RansomX, Gencirc, THHBIBC, Static AI, Malicious PE, aoplu, Detected, Malgent, Malware@#1rq9h18y4yut4, score, ai score=83, Autorave, unsafe, CLASSIC, vVdQeSDy+2E, FileCrypter, susgen, PossibleThreat, ZemsilF, @p0@a8k, Chgt, confidence, 100%) | ||
| md5 | 089428711dddec20eabf7732eea8fb8d | ||
| sha256 | ce6716a18c07d64059b961034a2ca46b1cae66892885d9e63063a0726a391461 | ||
| ssdeep | 24576:qozi/cws4dKqNKN59W8JY/AJs8tpfL3ZBXNXBfllfXRzQHwzHwcMZ5sm/IRImfwE:EcGviAWzrN3rzjWAkHpxMjrD | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 53 AntiVirus engines on VirusTotal as malicious |
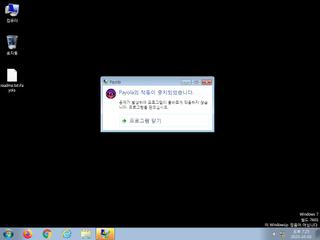
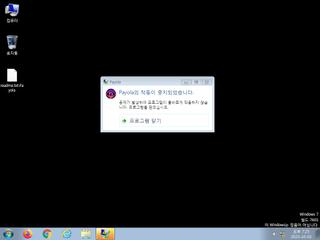
| watch | Appends a new file extension or content to 81 files indicative of a ransomware file encryption process |
| watch | Looks for the Windows Idle Time to determine the uptime |
| watch | Performs 81 file moves indicative of a ransomware file encryption process |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates (office) documents on the filesystem |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | Queries for the computername |
Rules (7cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (upload) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (upload) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none