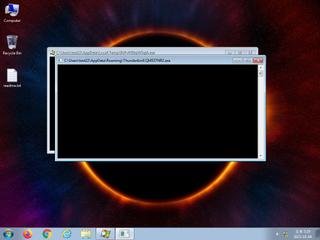
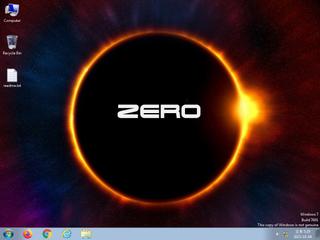
ScreenShot
| Created | 2023.10.04 17:32 | Machine | s1_win7_x6403 |
| Filename | 9UFv05EkjiW3qlA.exe | ||
| Type | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 44 detected (malicious, high confidence, Krypt, GenericRXWI, Vt8c, DropperX, Attribute, HighConfidence, score, Vwhl, Gen2, moderate, Generic ML PUA, Static AI, Malicious PE, twon, ai score=83, GH@60rvah, Phonzy, unsafe, dGZlOgwTO, kFakrH0A, ZemsilF, @pW@ayX86De, confidence, 100%) | ||
| md5 | 8830f7efe68fddb04c438f9aa1de2dba | ||
| sha256 | 55e8777df222fc3d6fccd14c60d1aa21ebfb7d91a50b8959e5b54e10fdf8a9fd | ||
| ssdeep | 49152:lluK1ytb+UC8AcqHag6tUDGBJseZHonFZbBZSGJv5pRGzO8KRi6hZSpm4/HScWnr: | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (13cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 44 AntiVirus engines on VirusTotal as malicious |
| watch | One or more of the buffers contains an embedded PE file |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | One or more processes crashed |
| info | Queries for the computername |
Rules (14cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Emotet_2_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none