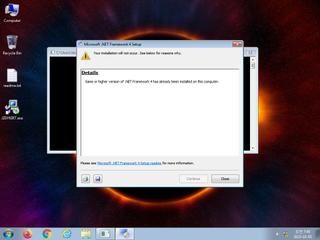
ScreenShot
| Created | 2023.10.05 07:51 | Machine | s1_win7_x6403 |
| Filename | rjFcwBLmZM9M3y7.exe | ||
| Type | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 41 detected (malicious, high confidence, Krypt, unsafe, Save, Attribute, HighConfidence, score, DropperX, dGZlOgwTO, kFakrH0A, Gen2, PackedNET, moderate, MsilDrop, twon, GH@60rvah, Detected, GenericRXWI, ai score=85, Binder, Static AI, Malicious PE, ZemsilF, FoW@aWB@evn, confidence, 100%) | ||
| md5 | 5d4392b56aa4ebac400bbe86fe5d0767 | ||
| sha256 | a604eed1325b12671370e268783cfa74f8675a468492ff98416187d73768b4af | ||
| ssdeep | 49152:o3s23i7y2K9TYDnORn+JuXbOoGlQXlSHcBA5TkfZnIZirM5RxivYp: | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (22cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 41 AntiVirus engines on VirusTotal as malicious |
| watch | Appends a known CryptoMix ransomware file extension to files that have been encrypted |
| watch | Attempts to access Bitcoin/ALTCoin wallets |
| watch | Executes one or more WMI queries |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Expresses interest in specific running processes |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Looks up the external IP address |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Searches running processes potentially to identify processes for sandbox evasion |
| notice | Sends data using the HTTP POST Method |
| notice | Steals private information from local Internet browsers |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Queries for the computername |
Rules (17cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | Network_Downloader | File Downloader | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (download) |
| info | bmp_file_format | bmp file format | binaries (download) |
| info | icon_file_format | icon file format | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (6cnts) ?
Suricata ids
ET POLICY External IP Lookup ip-api.com
ET HUNTING Observed Malicious Filename in Outbound POST Request (Information.txt)
ET HUNTING PNG in HTTP POST (Outbound)
ET HUNTING Observed Malicious Filename in Outbound POST Request (Information.txt)
ET HUNTING PNG in HTTP POST (Outbound)
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none