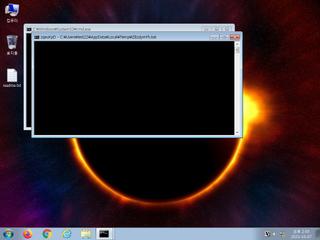
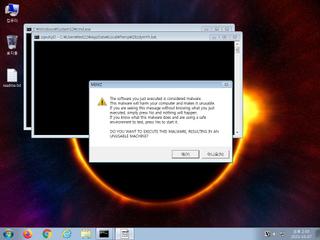
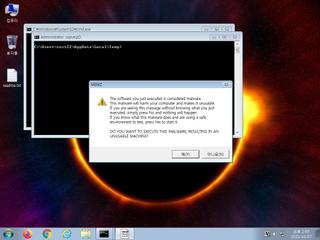
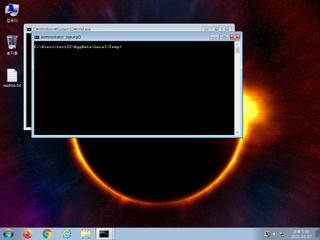
ScreenShot
| Created | 2023.10.07 14:48 | Machine | s1_win7_x6402 |
| Filename | ZBzdymFh.bat | ||
| Type | ASCII text, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 36 detected (Memz, Save, Zmem, Malicious, score, hkfymg, ExpKit, Gen2, KillAll, BatDrp, Malware@#10ov8inbnn3yr, Starter, Detected, CLASSIC, ai score=84) | ||
| md5 | 44fbd58c401a7786da2e8b6a6291379e | ||
| sha256 | d8b47727ea05305ad396977b336c3bfc86ae122cdde01976fa9b0c3a7c2d3f24 | ||
| ssdeep | 192:vOyUySl0UaDz2gWsIzlmj+BxZ3yqueWQx0lZicyC8Sh31xcjBzyxwn7AVhllz3:vVODaDSHMql3yqlxy5L1xcjwrlz3 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 36 AntiVirus engines on VirusTotal as malicious |
| watch | Drops a binary and executes it |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | One or more processes crashed |
Rules (37cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Suspicious_Obfuscation_Script_2 | Suspicious obfuscation script (e.g. executable files) | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Network_Downloader | File Downloader | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsPE32 | (no description) | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|