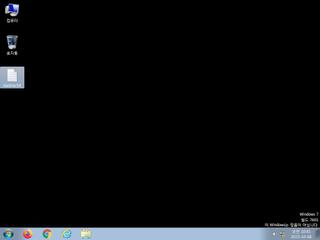
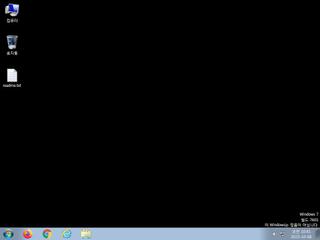
ScreenShot
| Created | 2023.10.08 10:45 | Machine | s1_win7_x6401 |
| Filename | Lopbf.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 50 detected (Common, Noon, malicious, high confidence, GenericKD, Artemis, V3id, RansomX, confidence, 100%, Attribute, HighConfidence, score, DropperX, Gencirc, ynvpq, Static AI, Malicious PE, ABRisk, BCJG, ai score=83, Wacatac, AgentTesla, Detected, ZemsilCO, Wm0@aWUCuPd, unsafe, Chgt, R002H0DJ423, CLOUD, susgen, GenKryptik, GLEY) | ||
| md5 | 5399d7a2060eca17c4c1648fd6b09505 | ||
| sha256 | 3751dae5d0813f6ec2fcc253c65854ddad340be058b199f4eb0a540bbf878efe | ||
| ssdeep | 12288:Xv4dLIwm2JMSzEM57yLx2j5xhvFTyTFiPVZqsXWryQW0jy8oWRfzp0KUu:XvAEw7t5HFmTANZqsXW2k | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (14cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 50 AntiVirus engines on VirusTotal as malicious |
| watch | A process attempted to delay the analysis task. |
| watch | Communicates with host for which no DNS query was performed |
| watch | Looks for the Windows Idle Time to determine the uptime |
| watch | One or more of the buffers contains an embedded PE file |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (upload) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Suricata ids
ET INFO Executable Download from dotted-quad Host
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none