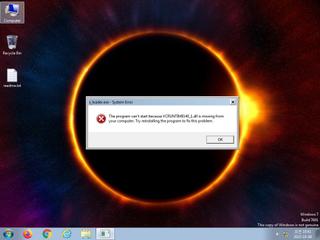
ScreenShot
| Created | 2023.10.08 10:47 | Machine | s1_win7_x6403 |
| Filename | x_loader.exe | ||
| Type | PE32+ executable (GUI) x86-64, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 25 detected (GenericKD, BadFile, Vmq1, malicious, confidence, 100%, Attribute, HighConfidence, high confidence, score, SMOKELOADER, YXDJDZ, Static AI, Malicious PE, ai score=87, Caynamer, ScarletFlash, unsafe, PossibleThreat, PALLAS) | ||
| md5 | 28008ae8515c137603e3cb0a14c38795 | ||
| sha256 | ca7f33e03be24e55e21620023e553a10975de033ae2ccdf82eb1b4066f570fe2 | ||
| ssdeep | 1536:7vach4C5miOAbFwwu6jSvhQrl4wRI/fun9auyR/M96i+ndOFleMYubd+pkuGRNA2:Dq84g3uFhQoAyR/g+nkBYOluhMHHDZ | ||
| imphash | c262573045b48eb83cfbc0d475b9abcd | ||
| impfuzzy | 24:U99JETcDLV8vaL6zhLTwKOYgMUiJyWPWUyWNwxlHySPDMyrQSLaJLocADzAZhJCT:UpV8vaLu1pxNilHVwaQSLw1+Yj2BSA | ||
Network IP location
Signature (2cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 25 AntiVirus engines on VirusTotal as malicious |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x140009000 FreeLibrary
0x140009008 LoadLibraryA
0x140009010 SetLastError
0x140009018 HeapAlloc
0x140009020 HeapFree
0x140009028 GetProcessHeap
0x140009030 GetNativeSystemInfo
0x140009038 VirtualAlloc
0x140009040 VirtualProtect
0x140009048 VirtualFree
0x140009050 GetProcAddress
0x140009058 IsBadReadPtr
0x140009060 GetStartupInfoW
0x140009068 IsDebuggerPresent
0x140009070 InitializeSListHead
0x140009078 GetSystemTimeAsFileTime
0x140009080 GetCurrentThreadId
0x140009088 GetCurrentProcessId
0x140009090 QueryPerformanceCounter
0x140009098 IsProcessorFeaturePresent
0x1400090a0 TerminateProcess
0x1400090a8 GetCurrentProcess
0x1400090b0 SetUnhandledExceptionFilter
0x1400090b8 UnhandledExceptionFilter
0x1400090c0 RtlVirtualUnwind
0x1400090c8 RtlLookupFunctionEntry
0x1400090d0 RtlCaptureContext
0x1400090d8 GetModuleHandleW
VCRUNTIME140.dll
0x1400090e8 _CxxThrowException
0x1400090f0 strstr
0x1400090f8 __C_specific_handler
0x140009100 __std_exception_copy
0x140009108 memcpy
0x140009110 __std_exception_destroy
0x140009118 __current_exception_context
0x140009120 memset
0x140009128 __current_exception
VCRUNTIME140_1.dll
0x140009138 __CxxFrameHandler4
api-ms-win-crt-time-l1-1-0.dll
0x140009250 _time64
api-ms-win-crt-utility-l1-1-0.dll
0x140009260 rand
0x140009268 srand
api-ms-win-crt-heap-l1-1-0.dll
0x140009148 _set_new_mode
0x140009150 _callnewh
0x140009158 realloc
0x140009160 malloc
0x140009168 free
api-ms-win-crt-stdio-l1-1-0.dll
0x140009220 __stdio_common_vfprintf
0x140009228 __acrt_iob_func
0x140009230 __stdio_common_vsprintf
0x140009238 _set_fmode
0x140009240 __p__commode
api-ms-win-crt-runtime-l1-1-0.dll
0x140009198 _register_thread_local_exe_atexit_callback
0x1400091a0 _c_exit
0x1400091a8 _cexit
0x1400091b0 _exit
0x1400091b8 _initialize_onexit_table
0x1400091c0 _register_onexit_function
0x1400091c8 _crt_atexit
0x1400091d0 terminate
0x1400091d8 exit
0x1400091e0 _initterm
0x1400091e8 _get_narrow_winmain_command_line
0x1400091f0 _initialize_narrow_environment
0x1400091f8 _configure_narrow_argv
0x140009200 _seh_filter_exe
0x140009208 _initterm_e
0x140009210 _set_app_type
api-ms-win-crt-math-l1-1-0.dll
0x140009188 __setusermatherr
api-ms-win-crt-locale-l1-1-0.dll
0x140009178 _configthreadlocale
EAT(Export Address Table) is none
KERNEL32.dll
0x140009000 FreeLibrary
0x140009008 LoadLibraryA
0x140009010 SetLastError
0x140009018 HeapAlloc
0x140009020 HeapFree
0x140009028 GetProcessHeap
0x140009030 GetNativeSystemInfo
0x140009038 VirtualAlloc
0x140009040 VirtualProtect
0x140009048 VirtualFree
0x140009050 GetProcAddress
0x140009058 IsBadReadPtr
0x140009060 GetStartupInfoW
0x140009068 IsDebuggerPresent
0x140009070 InitializeSListHead
0x140009078 GetSystemTimeAsFileTime
0x140009080 GetCurrentThreadId
0x140009088 GetCurrentProcessId
0x140009090 QueryPerformanceCounter
0x140009098 IsProcessorFeaturePresent
0x1400090a0 TerminateProcess
0x1400090a8 GetCurrentProcess
0x1400090b0 SetUnhandledExceptionFilter
0x1400090b8 UnhandledExceptionFilter
0x1400090c0 RtlVirtualUnwind
0x1400090c8 RtlLookupFunctionEntry
0x1400090d0 RtlCaptureContext
0x1400090d8 GetModuleHandleW
VCRUNTIME140.dll
0x1400090e8 _CxxThrowException
0x1400090f0 strstr
0x1400090f8 __C_specific_handler
0x140009100 __std_exception_copy
0x140009108 memcpy
0x140009110 __std_exception_destroy
0x140009118 __current_exception_context
0x140009120 memset
0x140009128 __current_exception
VCRUNTIME140_1.dll
0x140009138 __CxxFrameHandler4
api-ms-win-crt-time-l1-1-0.dll
0x140009250 _time64
api-ms-win-crt-utility-l1-1-0.dll
0x140009260 rand
0x140009268 srand
api-ms-win-crt-heap-l1-1-0.dll
0x140009148 _set_new_mode
0x140009150 _callnewh
0x140009158 realloc
0x140009160 malloc
0x140009168 free
api-ms-win-crt-stdio-l1-1-0.dll
0x140009220 __stdio_common_vfprintf
0x140009228 __acrt_iob_func
0x140009230 __stdio_common_vsprintf
0x140009238 _set_fmode
0x140009240 __p__commode
api-ms-win-crt-runtime-l1-1-0.dll
0x140009198 _register_thread_local_exe_atexit_callback
0x1400091a0 _c_exit
0x1400091a8 _cexit
0x1400091b0 _exit
0x1400091b8 _initialize_onexit_table
0x1400091c0 _register_onexit_function
0x1400091c8 _crt_atexit
0x1400091d0 terminate
0x1400091d8 exit
0x1400091e0 _initterm
0x1400091e8 _get_narrow_winmain_command_line
0x1400091f0 _initialize_narrow_environment
0x1400091f8 _configure_narrow_argv
0x140009200 _seh_filter_exe
0x140009208 _initterm_e
0x140009210 _set_app_type
api-ms-win-crt-math-l1-1-0.dll
0x140009188 __setusermatherr
api-ms-win-crt-locale-l1-1-0.dll
0x140009178 _configthreadlocale
EAT(Export Address Table) is none