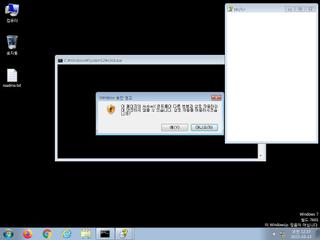
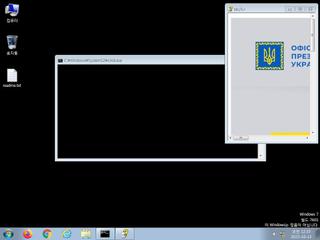
ScreenShot
| Created | 2023.10.13 00:35 | Machine | s1_win7_x6401 |
| Filename | dovidka.chm | ||
| Type | MS Windows HtmlHelp Data | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 38 detected (GenericKD, CVE-2019-0541, Malicious, score, TOPIS, PMkBg2JzqSK, MulDrop19, CHMDrop, ai score=100, GrayWare, Unc1151, Malware@#1iqsbfr3047p2, WinLNK, Detected, Agen, Cujl) | ||
| md5 | 2556a9e1d5e9874171f51620e5c5e09a | ||
| sha256 | 7f0511b09b1ab3a64c8827dd8af017acbf7d2688db31a5d98fea8a5029a89d56 | ||
| ssdeep | 6144:6hK9QF9IF78JuiKgnheEVfh+x6I/c0mGkBZ6w5+2yrBnx:d9QFq78JuiBnheEVqvcBZ6ws7nx | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (17cnts)
| Level | Description |
|---|---|
| danger | The process wscript.exe wrote an executable file to disk which it then attempted to execute |
| danger | File has been identified by 38 AntiVirus engines on VirusTotal as malicious |
| watch | A process attempted to delay the analysis task. |
| watch | Drops a binary and executes it |
| watch | Installs itself for autorun at Windows startup |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates a shortcut to an executable file |
| notice | Creates executable files on the filesystem |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Command line console output was observed |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | chm_file_format | chm file format | binaries (upload) |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|