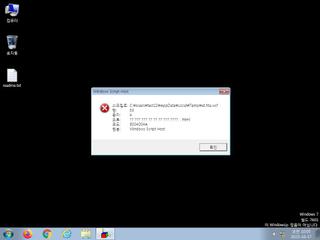
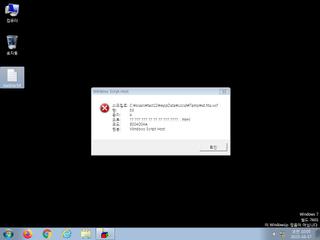
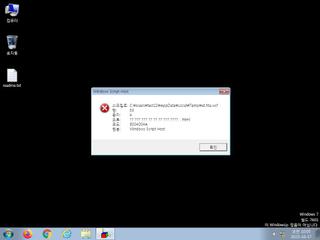
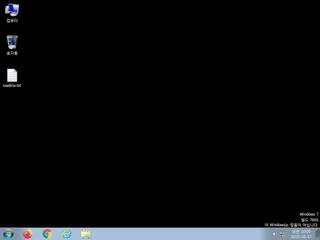
ScreenShot
| Created | 2023.10.17 10:07 | Machine | s1_win7_x6401 |
| Filename | at.hta | ||
| Type | HTML document, ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 26 detected (Valyria, Malicious, score, jpdglv, Xdkl, VPLT, DownLoader46, Detected, Eldorado, TOPIS, RXmrIh5jYAI, ai score=82) | ||
| md5 | b3a69d39ea2f074e520077721b475d51 | ||
| sha256 | 8e28ddc558064889072da509008e162887252a6237d305b528620508b450f725 | ||
| ssdeep | 192:WqgAUxKcGb+e64JVHzWPUgPYL1eKfTQhDcqsOHQXhSnP:dgA/RFOf | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (2cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 26 AntiVirus engines on VirusTotal as malicious |
| info | One or more processes crashed |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|