ScreenShot
| Created | 2023.10.17 10:38 | Machine | s1_win7_x6403_us |
| Filename | opt-63.js | ||
| Type | ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 27677b638817a290b98a867a960e28a1 | ||
| sha256 | 6fe4215a7d9dfb0827a2a3983243b740b281284747a373a9916d07817a5de88e | ||
| ssdeep | 6144:9j38P9IwPaHP79bvi5u9r9pMrSuyL3z8OF9Xk48iS+dxEDDstMpe:JBLzdk+dxE8tM0 | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (17cnts)
| Level | Description |
|---|---|
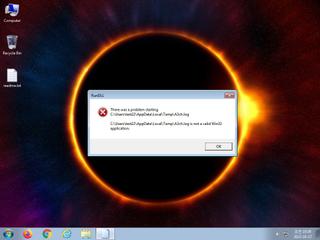
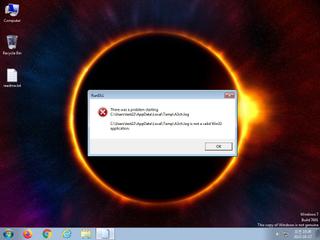
| danger | The process wscript.exe wrote an executable file to disk which it then attempted to execute |
| watch | Attempts to create or modify system certificates |
| watch | Communicates with host for which no DNS query was performed |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process wscript.exe |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | Wscript.exe initiated network communications indicative of a script based payload download |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Creates a suspicious process |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Command line console output was observed |
| info | One or more processes crashed |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (5cnts) ?
Suricata ids
ET POLICY curl User-Agent Outbound
ET HUNTING curl User-Agent to Dotted Quad
ET HUNTING curl User-Agent to Dotted Quad