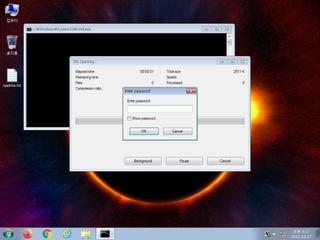
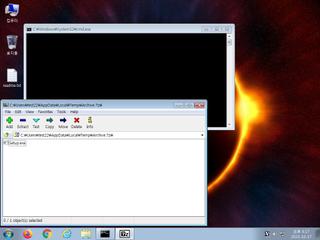
ScreenShot
| Created | 2023.10.17 16:28 | Machine | s1_win7_x6402 |
| Filename | Archive.7z | ||
| Type | 7-zip archive data, version 0.4 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 14cf80a7fd8a77c3eaed98b8ec615eb4 | ||
| sha256 | c5d36d14ec04f6a568172a2a91959b17dc768c41dc6bc9486d975d41056ac7b0 | ||
| ssdeep | 49152:+DFo8pF6h1toD9tvTKsQHCBLPnHGS9CozJYPBAmu9FXooJtewXmR:+DFRF6nA3K8HGSkodsGm8PLjmR | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (14cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| warning | Generates some ICMP traffic |
| watch | Communicates with host for which no DNS query was performed |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Looks up the external IP address |
| notice | Performs some HTTP requests |
| notice | Resolves a suspicious Top Level Domain (TLD) |
| notice | Sends data using the HTTP POST Method |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (146cnts) ?
Suricata ids
ET DNS Query to a *.top domain - Likely Hostile
SURICATA Applayer Mismatch protocol both directions
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io)
ET DROP Spamhaus DROP Listed Traffic Inbound group 7
ET MALWARE Win32/BeamWinHTTP CnC Activity M2 (GET)
ET INFO Observed External IP Lookup Domain in TLS SNI (api .myip .com)
ET INFO Executable Download from dotted-quad Host
ET HUNTING Suspicious services.exe in URI
ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016
ET INFO HTTP Request to a *.top domain
ET POLICY PE EXE or DLL Windows file download HTTP
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO TLS Handshake Failure
ET HUNTING Possible EXE Download From Suspicious TLD
ET INFO Observed External IP Lookup Domain (api .2ip .ua in TLS SNI)
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (Token)
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (External IP)
ET POLICY External IP Address Lookup DNS Query (2ip .ua)
ET MALWARE Win32/Stealc Requesting plugins Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with plugins Config
ET MALWARE Win32/Stealc Submitting System Information to C2
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET INFO Microsoft net.tcp Connection Initialization Activity
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET MALWARE [ANY.RUN] RedLine Stealer Related (MC-NMF Authorization)
ET MALWARE Redline Stealer TCP CnC Activity - MSValue (Outbound)
ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (Activity)
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET POLICY IP Check Domain (iplogger .org in DNS Lookup)
ET MALWARE Win32/Stealc Requesting browsers Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with browsers Config
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET USER_AGENTS Suspicious User Agent (Microsoft Internet Explorer)
ET MALWARE Potential Dridex.Maldoc Minimal Executable Request
ET MALWARE Win32/Vodkagats Loader Requesting Payload
ET INFO Packed Executable Download
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (Exfiltration)
ET INFO Observed Telegram Domain (t .me in TLS SNI)
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
ET MALWARE Win32/Filecoder.STOP Variant Request for Public Key
ET MALWARE Win32/Filecoder.STOP Variant Public Key Download
ET POLICY IP Check Domain (iplogger .org in TLS SNI)
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET INFO Dotted Quad Host ZIP Request
ET MALWARE Redline Stealer Activity (Response)
ET MALWARE Redline Stealer TCP CnC Activity - MSValue (Response)
ET MALWARE Single char EXE direct download likely trojan (multiple families)
ET MALWARE Amadey CnC Check-In
ET MALWARE Win32/Amadey Bot Activity (POST) M2
ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2
ET MALWARE Possible Kelihos.F EXE Download Common Structure
SURICATA Applayer Mismatch protocol both directions
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io)
ET DROP Spamhaus DROP Listed Traffic Inbound group 7
ET MALWARE Win32/BeamWinHTTP CnC Activity M2 (GET)
ET INFO Observed External IP Lookup Domain in TLS SNI (api .myip .com)
ET INFO Executable Download from dotted-quad Host
ET HUNTING Suspicious services.exe in URI
ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016
ET INFO HTTP Request to a *.top domain
ET POLICY PE EXE or DLL Windows file download HTTP
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO TLS Handshake Failure
ET HUNTING Possible EXE Download From Suspicious TLD
ET INFO Observed External IP Lookup Domain (api .2ip .ua in TLS SNI)
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (Token)
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (External IP)
ET POLICY External IP Address Lookup DNS Query (2ip .ua)
ET MALWARE Win32/Stealc Requesting plugins Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with plugins Config
ET MALWARE Win32/Stealc Submitting System Information to C2
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET INFO Microsoft net.tcp Connection Initialization Activity
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET MALWARE [ANY.RUN] RedLine Stealer Related (MC-NMF Authorization)
ET MALWARE Redline Stealer TCP CnC Activity - MSValue (Outbound)
ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (Activity)
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET POLICY IP Check Domain (iplogger .org in DNS Lookup)
ET MALWARE Win32/Stealc Requesting browsers Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with browsers Config
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET USER_AGENTS Suspicious User Agent (Microsoft Internet Explorer)
ET MALWARE Potential Dridex.Maldoc Minimal Executable Request
ET MALWARE Win32/Vodkagats Loader Requesting Payload
ET INFO Packed Executable Download
ET MALWARE [ANY.RUN] RisePro TCP v.0.x (Exfiltration)
ET INFO Observed Telegram Domain (t .me in TLS SNI)
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
ET MALWARE Win32/Filecoder.STOP Variant Request for Public Key
ET MALWARE Win32/Filecoder.STOP Variant Public Key Download
ET POLICY IP Check Domain (iplogger .org in TLS SNI)
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET INFO Dotted Quad Host ZIP Request
ET MALWARE Redline Stealer Activity (Response)
ET MALWARE Redline Stealer TCP CnC Activity - MSValue (Response)
ET MALWARE Single char EXE direct download likely trojan (multiple families)
ET MALWARE Amadey CnC Check-In
ET MALWARE Win32/Amadey Bot Activity (POST) M2
ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2
ET MALWARE Possible Kelihos.F EXE Download Common Structure