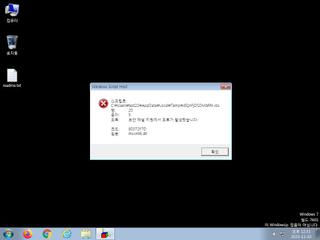
ScreenShot
| Created | 2023.11.03 12:33 | Machine | s1_win7_x6401 |
| Filename | JEQnFjDSDMbRhl.vbs | ||
| Type | ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 3acbcc1e0e59f0fa67e43c7e33a413c0 | ||
| sha256 | 966b73b3418a9a23ce25abedcfa732fcf1e1b54a1b315e710f02e402d4d55489 | ||
| ssdeep | 384:OtyWv9vIVvmxH6UzVSUSTUaUmUa047YeCVZWvHuVmqryqyLy+y008xUjK4:y9cmVlHPzjVZWW5n | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (3cnts)
| Level | Description |
|---|---|
| watch | Network communications indicative of a potential document or script payload download was initiated by the process wscript.exe |
| watch | Wscript.exe initiated network communications indicative of a script based payload download |
| info | One or more processes crashed |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|
Suricata ids
ET INFO DYNAMIC_DNS Query to a *.getmyip .com Domain
ET INFO TLS Handshake Failure
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO TLS Handshake Failure
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)