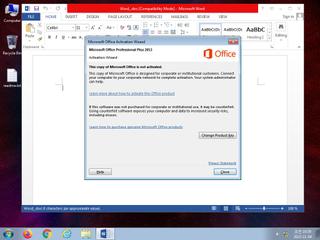
ScreenShot
| Created | 2023.11.04 10:44 | Machine | s1_win7_x6403 |
| Filename | Word_.doc | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Template: Normal, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Jul 11 13:57:00 2019, Last Saved Time/Date: Th | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 18 detected (malicious, high confidence, score, OLE2, Alien, druvzi, MacroS, AutorunMacro, Static AI, Malicious OLE, ABRisk, PADJ, qqxhz, Sadoca, Detected) | ||
| md5 | 75d7d706c41a6eb2d5a5161a24733999 | ||
| sha256 | 3d06c902f3360fffb06ee9a80b29c6764fc3e1676ce58a80dc684d3da3aa7f0c | ||
| ssdeep | 768:4nkOPn5317q1yV73Q0FYX7xByUQJb+wU3yXx0vbOH:pOPqowLSZ1+dyu | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | File has been identified by 18 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | Word document hooks document open |
| info | Office document has indirect calls |
| info | One or more processes crashed |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |