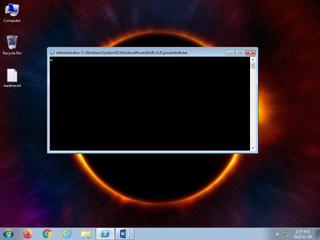
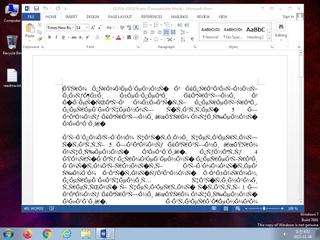
ScreenShot
| Created | 2023.11.08 08:04 | Machine | s1_win7_x6403 |
| Filename | d12934-0202334.doc | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: Admin, Template: Normal.dotm, Last Saved By: Admin, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | eac138b49c6f90896c9af5cbc8fe38b8 | ||
| sha256 | 44e593c98acaf52aee91c09fe00fa196668351783fc8a623fc1da5325635130f | ||
| ssdeep | 384:t68NWgtQziS8px8SMDVvHLZTlteZoN0j:t68N5X3y9HH | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (21cnts)
| Level | Description |
|---|---|
| danger | Connects to IP addresses that are no longer responding to requests (legitimate services will remain up-and-running usually) |
| danger | The processes winword.exe |
| watch | A command shell or script process was created by an unexpected parent process |
| watch | Communicates with host for which no DNS query was performed |
| watch | One or more non-whitelisted processes were created |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates (office) documents on the filesystem |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Creates hidden or system file |
| notice | Terminates another process |
| notice | Word document hooks document open |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (7cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Contains_VBA_macro_code | Detect a MS Office document with embedded VBA macro code [binaries] | binaries (upload) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |
| info | PowerShell | PowerShell script | scripts |