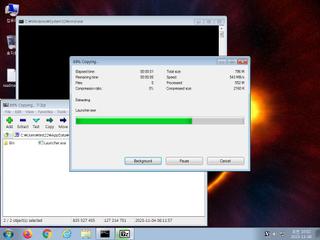
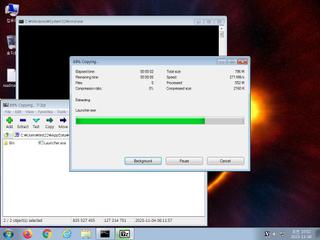
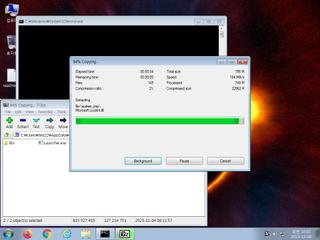
ScreenShot
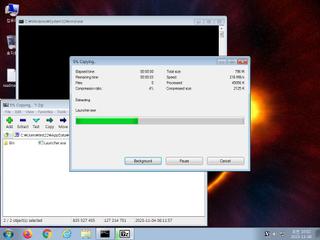
| Created | 2023.11.08 10:05 | Machine | s1_win7_x6402 |
| Filename | Launcher_Password_1234.rar | ||
| Type | RAR archive data, v5 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 1 detected (Artemis) | ||
| md5 | 128e1564f4afaf681a3572f8667f6bd4 | ||
| sha256 | f2498016ed30f0cc216d9ea9810acf21e6f62b63a999ad69941dfacc75d26bb3 | ||
| ssdeep | 786432:FPPM86ONdg6V+38tuT46ShyuesGuzghb6xhb49aC+YnAJR6wCKcv:FnM8rY6V+stVhjeS6b6xJaagwbcv | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (7cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
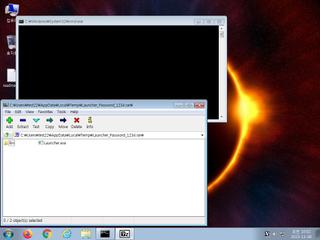
| notice | Creates executable files on the filesystem |
| notice | File has been identified by one AntiVirus engine on VirusTotal as malicious |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|