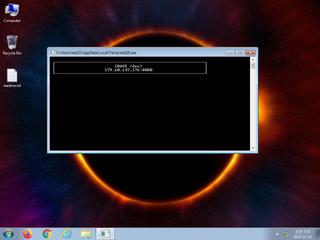
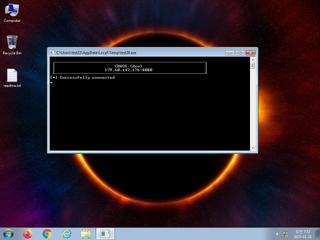
ScreenShot
| Created | 2023.11.21 07:55 | Machine | s1_win7_x6403 |
| Filename | test20.exe | ||
| Type | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 16 detected (AIDetectMalware, RemoteAdmin, Chaos, malicious, high confidence, a variant of WinGo, D potentially unsafe, Detected, Eldorado, score, Khaosz, R575825, susgen) | ||
| md5 | fbd70a366b8f1c3e25e080cdd553930f | ||
| sha256 | f32a707eb324627cf5bd3904d8db2acb9bd71b506526d1aa153874b40f359452 | ||
| ssdeep | 49152:l/oG3crb/THvO90dL3BmAFd4A64nsfJsH4xjkNyCEHQPaHOKNMKVk9B/omcQHEKy:f3LwGf3uuEmRjU+G | ||
| imphash | 9cbefe68f395e67356e2a5d8d1b285c0 | ||
| impfuzzy | 24:UbVjhNwO+VuT2oLtXOr6kwmDruMztxdEr6tP:KwO+VAXOmGx0oP | ||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | Detects the presence of Wine emulator |
| watch | File has been identified by 16 AntiVirus engines on VirusTotal as malicious |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Sends data using the HTTP POST Method |
| info | Command line console output was observed |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (5cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Suricata ids
ET MALWARE CHAOS RAT CnC Server Status Check
ET MALWARE CHAOS RAT Client Checkin
ET USER_AGENTS Go HTTP Client User-Agent
ET MALWARE Win32/Khaosz.A!MTB Checkin
ET MALWARE CHAOS RAT Client Checkin
ET USER_AGENTS Go HTTP Client User-Agent
ET MALWARE Win32/Khaosz.A!MTB Checkin
PE API
IAT(Import Address Table) Library
kernel32.dll
0x8bf420 WriteFile
0x8bf428 WriteConsoleW
0x8bf430 WaitForMultipleObjects
0x8bf438 WaitForSingleObject
0x8bf440 VirtualQuery
0x8bf448 VirtualFree
0x8bf450 VirtualAlloc
0x8bf458 SwitchToThread
0x8bf460 SuspendThread
0x8bf468 SetWaitableTimer
0x8bf470 SetUnhandledExceptionFilter
0x8bf478 SetProcessPriorityBoost
0x8bf480 SetEvent
0x8bf488 SetErrorMode
0x8bf490 SetConsoleCtrlHandler
0x8bf498 ResumeThread
0x8bf4a0 PostQueuedCompletionStatus
0x8bf4a8 LoadLibraryA
0x8bf4b0 LoadLibraryW
0x8bf4b8 SetThreadContext
0x8bf4c0 GetThreadContext
0x8bf4c8 GetSystemInfo
0x8bf4d0 GetSystemDirectoryA
0x8bf4d8 GetStdHandle
0x8bf4e0 GetQueuedCompletionStatusEx
0x8bf4e8 GetProcessAffinityMask
0x8bf4f0 GetProcAddress
0x8bf4f8 GetEnvironmentStringsW
0x8bf500 GetConsoleMode
0x8bf508 FreeEnvironmentStringsW
0x8bf510 ExitProcess
0x8bf518 DuplicateHandle
0x8bf520 CreateWaitableTimerExW
0x8bf528 CreateThread
0x8bf530 CreateIoCompletionPort
0x8bf538 CreateFileA
0x8bf540 CreateEventA
0x8bf548 CloseHandle
0x8bf550 AddVectoredExceptionHandler
EAT(Export Address Table) is none
kernel32.dll
0x8bf420 WriteFile
0x8bf428 WriteConsoleW
0x8bf430 WaitForMultipleObjects
0x8bf438 WaitForSingleObject
0x8bf440 VirtualQuery
0x8bf448 VirtualFree
0x8bf450 VirtualAlloc
0x8bf458 SwitchToThread
0x8bf460 SuspendThread
0x8bf468 SetWaitableTimer
0x8bf470 SetUnhandledExceptionFilter
0x8bf478 SetProcessPriorityBoost
0x8bf480 SetEvent
0x8bf488 SetErrorMode
0x8bf490 SetConsoleCtrlHandler
0x8bf498 ResumeThread
0x8bf4a0 PostQueuedCompletionStatus
0x8bf4a8 LoadLibraryA
0x8bf4b0 LoadLibraryW
0x8bf4b8 SetThreadContext
0x8bf4c0 GetThreadContext
0x8bf4c8 GetSystemInfo
0x8bf4d0 GetSystemDirectoryA
0x8bf4d8 GetStdHandle
0x8bf4e0 GetQueuedCompletionStatusEx
0x8bf4e8 GetProcessAffinityMask
0x8bf4f0 GetProcAddress
0x8bf4f8 GetEnvironmentStringsW
0x8bf500 GetConsoleMode
0x8bf508 FreeEnvironmentStringsW
0x8bf510 ExitProcess
0x8bf518 DuplicateHandle
0x8bf520 CreateWaitableTimerExW
0x8bf528 CreateThread
0x8bf530 CreateIoCompletionPort
0x8bf538 CreateFileA
0x8bf540 CreateEventA
0x8bf548 CloseHandle
0x8bf550 AddVectoredExceptionHandler
EAT(Export Address Table) is none