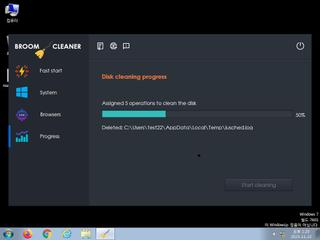
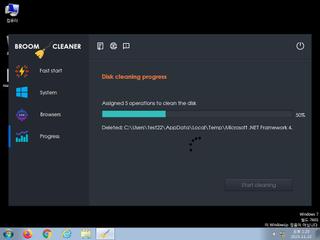
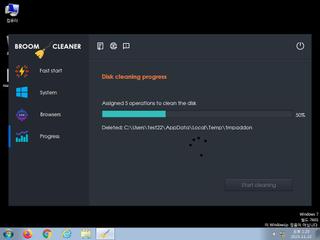
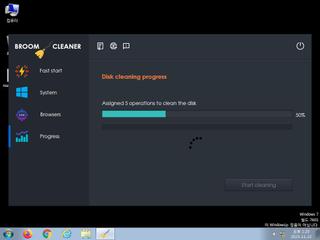
ScreenShot
| Created | 2023.11.22 13:29 | Machine | s1_win7_x6401 |
| Filename | allnewumm.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 50 detected (ShortLoader, MulDropNET, MSILZilla, GenericRXOO, Save, malicious, confidence, 100%, Ransomware, ZemsilF, @p0@aK5whFe, Attribute, HighConfidence, high confidence, score, Mokes, ILAgent, AGEN, R002C0DKL23, high, Detected, ai score=88, Kryptik, Eldorado, unsafe, GdSda, AntiVM, CLASSIC, Static AI, Malicious PE, susgen, GenKryptik, FFMZ, DropperX) | ||
| md5 | b1d5ab180b539da823cf40c7638d0286 | ||
| sha256 | fae531687cc458d8d7e504b81776514eec3cd9700891a1b873afa3748c84cc78 | ||
| ssdeep | 393216:Lexbl6e6TvVmR/i+W7n/+8HVi5vcPF07zvrRl:LexZpkmRa+W7n/p1i5KF0PrR | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (18cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 50 AntiVirus engines on VirusTotal as malicious |
| danger | Executed a process and injected code into it |
| watch | Attempts to identify installed AV products by installation directory |
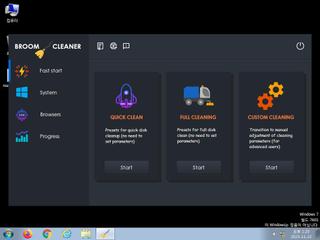
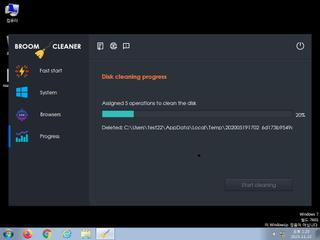
| watch | Deletes a large number of files from the system indicative of ransomware |
| watch | Deletes executed files from disk |
| watch | Detects VirtualBox through the presence of a file |
| watch | Drops 105 unknown file mime types indicative of ransomware writing encrypted files back to disk |
| watch | Tries to unhook Windows functions monitored by Cuckoo |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
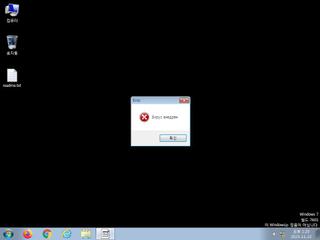
| info | One or more processes crashed |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (30cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | HermeticWiper_Zero | HermeticWiper | binaries (download) |
| danger | NPKI_Zero | File included NPKI | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | NSIS_Installer | Null Soft Installer | binaries (download) |
| warning | Suspicious_Obfuscation_Script | Suspicious obfuscation script | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | Javascript_Blob | use blob(Binary Large Objec) javascript | binaries (download) |
| info | bmp_file_format | bmp file format | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (download) |
| info | DllRegisterServer_Zero | execute regsvr32.exe | binaries (download) |
| info | icon_file_format | icon file format | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (download) |
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none